Introduction to Cybersecurity
Hackers, viruses, trojans, cybercrime….these are just some of the many reasons you need to invest in cybersecurity. If you think your business is safe from a data breach, you are dead wrong. Viruses can come alive in seconds and cripple systems. All major companies including AT&T, Apple, and Target have been victims of cybercrime. If you don’t take precautions today, you could be next tomorrow. In case this sounds like a trailer of some frightening movie, be rest assured that in the cyber world, life does imitate art many times.
Business owners are aware of cybercriminals are more sophisticated, but many companies think “It just can’t happen to me” only to be victims of a data breach, cyber fraud, or more. You need to put security measures in place to handle vulnerabilities. Large corporations may have more money to invest, but every business can take preventative measures where it is in terms of training staff, developing resources, or know-how. Criminals in the virtual world, much like the real, look for unlocked doors and windows of opportunity in your system. These signs can alert you if you are in need of Invest in cybersecurity solutions.
Best 17 Signs to Invest in Cybersecurity
Below are 17 signs to invest :
# 1 You Have been Phished
If you feel something fishy is going on when “trusted” websites start asking for sensitive information from you, you should not take the bait, and fall prey to a phishing fraudster. But, if you happen to be the catch of the day because you did not take proper precautions, be prepared to pay a heavy price for it. Phishing frauds provide cybercriminals with information to access credit cards and make off with your cash or worse still, steal your identity.
#2 Your credit card company reports fraudulent charges
Security solutions can only work if you act in time. If your credit card is breached, you will definitely be in the know. But you need to take action right away otherwise it will be a little too late. Business data once breached can lead to mounting losses, and this can be an even heavier burden to carry if you did not invest in cybersecurity information to start with.
#3 Unusually slow internet or computers that stall
Any unusual computer or internet activity could be an indication that your machine has been sending out a lot of traffic. Slow speed could also indicate the presence of a virus or malware on the computer. Check for pop-up ads that come up too often if you have ad-block in place and always be cautious when websites do not load properly.
#4 Programs run after you have left work or turned off your computer
This is an indication that your computer data has been breached. If you switched off the computer and you return to find it on or running programs you did not activate, it’s a good guess that you are a victim of cybercrime. Invest in Cybersecurity will ensure you are not left crying over spilled milk by protecting your password and encrypting sensitive information.
#5 Locked out accounts
This is another sure sign you are being hacked. If you are locked out of your email or social networking accounts like Facebook, LinkedIn or more, it’s time to invest some money in a good IT security program or invest in cybersecurity training for your staff.
Every business can only prosper if it remains secure. Getting locked out can mean two possible things:
1: Someone has tried to use brute force to open your account
2: Account has been compromised, and the hacker has changed your password
So, how can cybersecurity analysts help in such situations? Experts say keeping your device operating systems, firewalls, and antivirus software in place may be the key here. So, be safe rather than sorry and have your cybersecurity systems in place.
#6 You detect unusual activity
Hackers can create a better world by protecting systems and showcasing vulnerabilities. Unfortunately, they can also wreck a business and cause much harm, if disposed of in this direction. Always trust your intuition rather than acting rapidly without a plan. Hackers can make your computer dance to their tunes if they breach your system. From financial accounts to credit card information, nothing will remain safe from them. So, if your computer starts behaving in an out-of-ordinary fashion, look for signs of trouble.
This includes standard programs and files suddenly not opening or working correctly. Another indication is that files that were not deleted by you have vanished from the face of the screen or landed in the trash somehow. Another possible sign is that you cannot access programs using the usual password. If your computer password suddenly changes without any action on your part, it’s a sure sign your data has been compromised.
Another red flag is if there are one/more programs on your computer which you did not place there, to begin with. If the computer starts to dial up the internet, without any attempt from you to connect, this is another possible sign you are being hacked. Another warning bell is that file contents have changed without you having made any modifications to them. Printers not carrying out commands or jumbling pages could also be a potential warning signal.
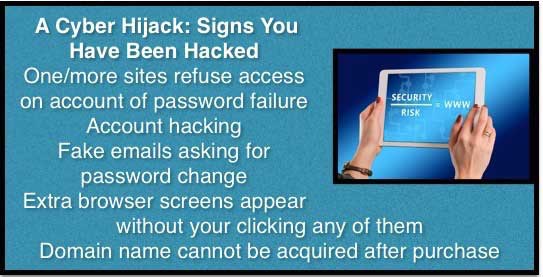
#7 Online signs are strong that your data has been compromised
This could be any of the following:
#8 Standard hacker malware or overrides are visible in your system
This includes fake virus messages, additional toolbars appearing in the browser carrying messages about offering you ”help” or multiple messages that spread across the screen. Another warning sign is that random and frequent pop-ups start to make their appearance on the computer. Bills are being sent to you for fake online purchases…this is exactly how you are being made to pay for not having invest in cybersecurity. Another sign is if people in your address list get fake emails from you.
#9 Random movements of your cursor are rapidly increasing
This is a sign that a human hacker has managed to control your cursor and he or she is playing a cat-and-mouse game with you. This can have serious repercussions if the hacker is able to access your files or manipulate the controls on your computer.
# 10 Unusual Google search results show someone has leaked out your confidential information
Google yourself. If you find some personal information online which you have not disclosed, this is a sign that someone has hacked your computer and stolen information about you. If the data is damaging your organization or personal reputation, this can be disastrous. Strictly confidential information on your computer or email messages containing important details about your organization’s work can be valuable to unscrupulous cyber criminals and unusual search engine results are a litmus test of how secure your personal information is. Spotting suspicious online activity is a surefire warning you need to rev up your cybersecurity protection.
Locking the door after the burglar has come in won’t solve the problem, a good cybersecurity package will.
Image source: pixabay.com
#11 Brute force cracking or trial and error crackers are trying their luck with you
A cracker tries to access your system using trial and error and no encryption software program is safe from this method. Don’t think the numbers will deter the cracker….a 56-bit key may have 256 possible keys meaning around seventy-two quadrillion key combinations before he or she gets the right one. So use software with as many bits as possible and get cracking on an encryption software program or IT security application which will protect you.
#12 Someone’s getting in through the back door
A backdoor refers to a network security hole in a software program. Backdoor may be present because someone has left the window open and if a cracker discovers this, he or she can unearth your key or password. So, make sure you have a cybersecurity program that covers your back or your password will become a passkey for unauthorized users.
#13 You don’t exactly come up with secure passwords
Image source: pixabay.com
If “Apple1234” is your idea of a password, you definitely need cybersecurity. Many password guessing programs are in place to crack your “secure” password so you are not safe. Even if you use random letters, numbers and symbols, the key needs to belong. If you are not exactly Einstein when it comes to creating passwords, cybersecurity programs need to be in place or time will hang heavy on your hands as attempts are made to fix the damage, relativity or no relativity! Another alternative is to offer passwordless authentication with passkeys.
#14 Security logs show a breach
If security logs show that devices other than your own have accessed your account, you are less than safe in the cyber world. Even if passwords change or stop working in an attempt to prevent “dictionary” cyber attacks, signs are strong that a cybercriminal is targeting you and you are in danger of a security breach.
Files containing art tags or hacker organization signatures are another potential sign of trouble in cyber-land. Many narcissistic hackers sign their work and the result is an altered file or there is a detailed view of files showing an unauthorized modification.
If you are noticing deleted files in your recycle bin. or software or task manager stops working/encounters an error, you are working on a less than secure system, and it’s time to switch to a good antivirus or Invest in cybersecurity installation.
#15 Unauthorized installations are on the rise
Suddenly, you notice new software, programs, shortcuts, toolbars or icons which were not installed by you. If drives are being shared when the permission for the same was not given or new network connections are in place despite your not having created it, a cybercriminal is definitely on the prowl.
#16 People receive “spam” from your account
Image source: pixabay.com
If people start receiving email malware or spam from you and someone is using your identity on social media, email or professional networking accounts, you need to secure your system, change your passwords and get a good cybersecurity program in place.
#17 You receive a warning from the system
If your PC beeps or starts sending warming messages or you see a fake virus, malware messages, you can definitely start contacting a cybersecurity specialist and take proactive steps to protect yourself. If your antivirus or anti-malware program has been disabled, this is positive indication hackers are up to no good using your system. If there is unusual TCP or UDP port action, as entered in utilities like TCP view, this is another alarm bell that can be your wake-up call.
Conclusion
A good security toolbox with firewalls, anti-spyware, antivirus, anti-malware, and encryption can be a successful cyber defense against unscrupulous hackers and cybercriminals. Even if you are not exactly the Newton of the virtual world, you can keep your Apple safe by invest in cybersecurity systems! Firewall, anti-spyware and antivirus work to block invasion whether the intrusion is from the hardware or the software side. Encryption ensures that hackers will not be able to prevail and anti-virus programs will block even the most determined trojans. Adding to the complexity in your computer, these cybersecurity precautions will safeguard you from the most vicious crackers and depraved hackers.
If you neglect to invest in cybersecurity, be prepared to face the consequences. It is estimated that around 30,000 websites are hacked each day and the number is slated to only increase as cybercriminals take the easy route to make money. Intercepting your sensitive data and penetrating your systems will definitely be tougher if you take safety precautions. A well-developed investment in cybersecurity systems will work like a lock on your virtual door and protect your system from unwanted intrusions. So, what are the different types of hacking you need to be aware of? Well, here is a pretty comprehensive list:
• Trojan Horse: Malware that harms your system from the inside out, much like the ancient Trojan horse in Troy
• DoS/Denial of Service: This is used to prevent internet users from accessing a specific website by hacking their system
• IP Spoofing: This offers cybercriminals unauthorized access to the system
• Fake Wireless Access Points: This is when the fake wireless points in your Wi-Fi hotspot are much like a gaping hole in the wall through which the hacker makes his or her entry and sets off with your data
• File naming tricks that mislead you towards clicking a certain malware file
• Smurf or attacks similar to DoS
• Server spoofing or when data is sent to server cache and there is redirecting of traffic to a computer of the hacker’s choice.
Just as a hacker has many weapons in his or her arsenal, so does the user or business being targeted. Invest in Cybersecurity is a necessary step forward if you want your official website or computer system to be secure. So, take that small step towards a giant leap for a secure cyber world.
Recommended Articles
This has been a guide to Invest in Cybersecurity. Here we discussed the Basic Concept of Cybersecurity and the Best 17 Signs to Invest in Cybersecurity. You can also go through our other suggested articles to learn more –