Updated March 14, 2023
What is User Datagram Protocol?
User Datagram Protocol is a connectionless, unreliable transport protocol that lies between the application and transport layers. It does not add anything to IP services except for providing a process to process communication instead of the host to host evidence. User Datagram Protocol transfers data in packet format, which has 8 bytes of the header that includes parameters like source port number, destination port number, total length, checksum each of 16 bits. UDP provides services like the process to process communication, connectionless services, flow control, error control, checksum, congestion control, encapsulation, and decapsulation, queuing, multiplexing, and demultiplexing.
Understanding User Datagram Protocol
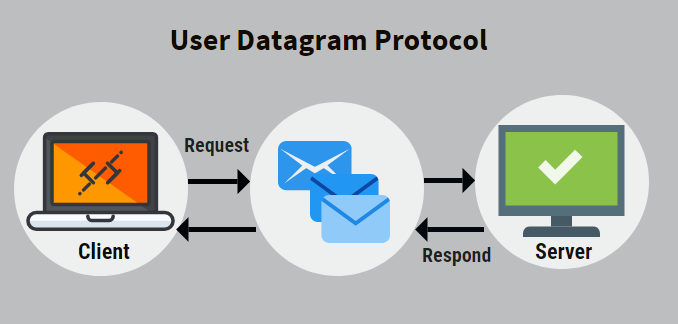
User datagram protocol (UDP) is a transport layer protocol in an open systems interconnection (OSI) for client-server network applications. UDP implements a simple transmission model. It, however, does not believe in handshaking in for reliability, order or data integrity.
UDP does not believe in error-checking or correction to avoid the time spent in processing at the network level. The UDP protocol does not monitor the order in which the packets are sent, and it permits these packets to be dropped and received in a different order than the one they were sent in. This helps UDP in better performance.
The network traffic of UDP is arranged in the form of datagrams. The datagrams are the smallest units consisting of one message unit. The header information is stored in the first eight units of a datagram. The remaining bytes of a UDP datagram consists of message data. Thus, eight units of the header information in a UDP datagram is divided into four fields of two bytes, each containing the source port number, the destination port number, the size of the datagram and the checksum.
- Source Port: Is a service access point or SAP used to indicate the local client’s session from where the packet originated.
- Destination Port: Is a service access point to indicate the client’s services request to the remote server.
- UDP length: The total size of the datagram consisting of UDP header information and payload data
- UDP Checksum: A checksum is to verify the originality of the payload data and ensure that routers or bridges in the network have not corrupted it. One of such checksum algorithm is the Standard Internet Checksum algorithm. It safeguards an application against receiving incorrect data in place of or in addition to whatever was sent.
What can you do with the User Datagram Protocol, and why is it Used?
Let us discuss what can we do with it and why it is being used:
- All application designers know that, unlike Transmission Control Protocol, User Datagram Protocol does not provide any reliability. If any packets are lost on the way, UDP will not retransmit those lost packets. This often is the main reason to consider transporting messages via UDP. UDP is basically used in applications in which there is no requirement of a reliable protocol for delivering messages by implementing appropriate protocol mechanisms in their applications.
- The best-effort service of UDP is unable to protect the datagram from datagram duplication. This means that sometimes an application tends to receive multiple copies of the same datagram, which UDP does not automatically filter. Therefore, the application designers are expected to verify that the application that is being used can gently handle the datagram duplicacy and implement mechanisms capable enough to filter out the duplicate datagrams received.
- Sometimes due to traffic, congestion, routing transients, mobility, etc., there might be a significant delay in some packets as compared to the other packets. This may lead to a disturbance in the order of the datagrams transmitted, and the order of datagrams arrived at the receiver. This leads to reordering, which can only be restored if the application has a mechanism to restore the datagrams order.
Advantages
Given below are the advantages mentioned:
- One of the exciting features of UDP is neither it needs to retransmit the packets that are lost while transmission, nor does it require any connection setup. Due to this feature, the data that is sent incurs less delay in being received by the receiver. This lower delay makes UDP appropriate to be used in delay-sensitive applications like audio and video.
- Multicast applications use UDP as they do point to multipoint. In the case of TCP is used for multicast applications, the sender needs to record the retransmissions/sending rate for multiple receivers, which would become highly complex.
- Much faster than TCP.
Disadvantages
Given below are the disadvantages mentioned:
- There is no guarantee of UDP.
- A packet might not be delivered or might be delivered multiple times and out of order without you getting any indication of it.
- UDP has no flow control or congestion control.
- UDP suffers from worse packet loss than TCP.
Conclusion
The service that User Datagram Protocol provides might be unreliable, providing no guarantee for delivery or protection from datagram duplication. Still, it is only because of this simplicity that using UDP reduces the overhead time, latency and prove very useful for applications requiring such features.
Recommended Articles
This has been a guide to User Datagram Protocol. Here we discussed the use of user datagram protocol, understanding, advantages, and disadvantages, respectively. You can also go through our other suggested articles to learn more –