Introduction to Security Testing
Security Testing for an application is an essential step in the software testing lifecycle. It controls unauthorized invasions in various application levels, such as the servers, the front-end application layer, the middleware modules, and network security. This testing is used to verify if the system or users with only proper Authentication can access the application. In contrast, those that fail the Authentication are restricted from using the application.
Here is a list of security flaws:
- A student management system is insecure if the ‘ Entry ‘ branch can edit the Exam information.
- If DEO (data entry operator) can produce ‘ reports, ‘an ERP scheme is unsafe.
- The online Website has no safety if it does not encrypt the Credit Card details of a client.
- Personalized software has insufficient safety when an SQL query finds actual user passwords.
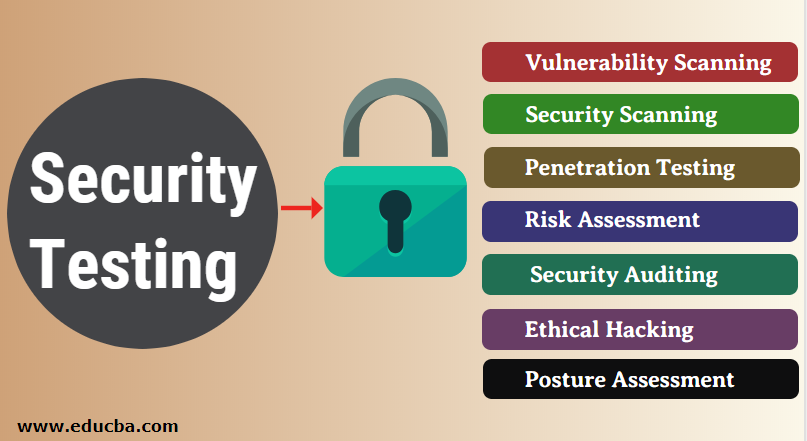
Types of Security Testing
The Open Source Security Testing Methodology Manual has seven principal safety tests.
- Vulnerability Scanning: This is performed via automated software to scan a system for known vulnerability signatures.
- Security Scanning: It includes identifying weaknesses in the network and system and offers alternatives for decreasing such hazards. For manual and automated scanning, this scanning can be done.
- Penetration Testing: This test simulates a malicious hacker attack. This examination includes analyzing a specific system to detect prospective vulnerabilities to internal hacking.
- Risk Assessment: This test includes analyzing the safety hazards observed in the company. The risks have low, medium, and high classifications. This test proposes risk reduction controls and actions.
- Security Auditing: The audit can be done online by line, code inspections, and operating systems for safety faults.
- Ethical Hacking: Ethical hacking is not the same as malignant hacking. Instead, ethical hacking aims to identify safety shortcomings in the organizational structure.
- Posture Assessment: This combines safety scanning, risk evaluations, and ethical hacking to show an overall safety position of an organization.
Methodologies of Security Testing
There are different methodologies of security testing:
- Tiger Box
- Black Box
- Gray Box
1. Tiger Box
This hacking is performed on a laptop with an OS and hacking tool collection. This test allows penetration and security testing operators to evaluate and attack vulnerabilities.
2. Black Box
Black Box Testing is a software testing method known to the tester as Behavioral Testing. In this way, the internal design of the test product is not known. Therefore, these exams can be either functional or not.
3. Gray Box
Gray Box Testing is a software testing technique that combines Black Box and White Box testing. Grey Box Testing is a method for testing the application or software product that has part of the inner working of an implementation.
How can we do Security Testing?
It has always been agreed that this cost will be increased if we postpone security testing following software implementation or deployment. In the earlier stages, security tests must be carried out in the SDLC life cycle. Let us look at the appropriate security procedures for each SDLC stage. For the input areas, the Tester can inspect the maximum lengths. This limitation can – not allow a hacker to include such malicious scripts.
- Requirements security assessment and abuse/misuse check.
- Analysis of security hazards for design. Test Plan development, including safety testing.
Top 10 Open Source Security Testing Tools
Below is the list of top Security Testing tools and their features. Of course, you can choose any tool based on your needs.
1. Wapiti
Wapiti is a powerful web application security test tool for assessing your web application safety. It conducts ‘ black box testing ‘ to check for potential vulnerabilities in web applications. It scans the web pages and injects testing information to monitor the safety deficiency during the testing phase. Wapiti defines multiple vulnerabilities for the support of GET and POST HTTP attacks. Wapiti is an application for commands that is difficult for beginners but simple for professionals. Therefore, the software needs a complete command understanding.
Features of Wapiti:
- XSS Injection
- Database Injection
- Detection of Command Execution.
- Injection CRLF
2. Zed Attack Proxy
The OWASP created the Zed Attack Proxy, commonly known as ZAP, ZAP, and with that, ZAP is open-source. Zed Attack Proxy Supported by Unix / Linux, Windows, and Mac OS, Zed Attack Proxy allows you to identify a range of vulnerabilities even during the development and testing stage in web applications. This test tool is easy to use, even while you are a penetration test beginner.
Features of Zed Attack:
- Zed Attack Proxy has an Automation Scanner and Authentication support.
- Zed Attack Proxy also has a Dynamic SSL Certificate and Web Socket Support.
3. Vega
Written in JAVA, Vega has a GUI. It is accessible on Linux, Mac OS, and Windows, which can help you. Vega is a free web application testing tool and Open Source platform. Vega can assist in finding and validating SQL Injection, Cross-Site Scripting (XSS), and other vulnerabilities. It can also be used to set preferences, like the number of path descendants and nodes per second and maximum and minimum requests per second.
Features of Vega:
- Vega has cross-Site Scripting.
- SQL Injection Validate.
4. W3af
W3af is a famous security testing framework for web applications. It provides an effective web application penetration testing platform developed using Python. This tool can identify over 200 internet application safety problems, such as Cross-Site Scripting and SQL injection. In addition, it monitors the following web-app vulnerabilities. W3af can be easily understood and used through GUI (Graphical User Interface) and console interfaces. The authentication modules also allow you to authenticate the Website.
Features of W3af:
- Multiple CORS defective settings.
- CSRF and a lot more vulnerability.
5. Skipfish
Skipfish is an internet application proctored test tool that remedies the site, checks for weaknesses on each page, and prepares the audit report. Skipfish is written in c language and is optimized to handle HTTP and leave minimum CPU footprints. The software claims to process 2 K requests per second without showing a CPU footprint. The tool also claims to offer high-quality benefits as it utilizes heuristics in web applications. The Skipfish safety assessment tool for internet applications is available for Linux, FreeBSD, macOS, and Windows operating systems.
6. SQLMap
Common web-based security testing tools, such as SQLMap, automate the process of detecting SQL injection vulnerabilities in a website’s database. Packaged with several features, the powerful test engine allows easy penetration and SQL injection testing on a Web application. SQLMap supports many databases, including MySQL, Oracle, PostgreSQL, Microsoft SQL, etc. In addition, the test tool supports six different methods of SQL injection.
7. Wfuzz
Wfuzz is another open-source tool that can be freely accessible on the market for a web-based security testing tool. This Testing Tool was developed in Python and is used for web applications for brute force. You need to operate on the command line interface when using Wfuzz because there is no GUI interface.
Features of the Wfuzz:
- Wifuzz supports multiple Injection points.
- The output of Wfuzz comes in HTML.
- It also has Multi-threading.
- It also has Multiple proxy support.
8. Metasploit
One of the most commonly used frameworks for penetration tests. Metasploit is an open-source testing platform allowing safety tests beyond risk assessment.
Features of the Metasploit:
- The structure is far better than that of the rivals.
- Many scenarios for mock infiltration functions
9. Acunetix
A complete automation penetration assessment tool to scan your websites for 4500 + vulnerabilities. Acunetix’s most striking feature is that it can rush thousands of pages without interruption.
Feature of Acunetix:
- It can readily produce many technical and compliance remedies.
- Scans of both open-source and personalized apps
- Deep scans for efficient scanning.
10. Grabber
Grabber is an open-source scanner to detect internet applications ‘ safety vulnerabilities. Small web applications such as forums and private Internet sites are mobile and can be scanned. However, Grabber is a small testing tool that takes longer to scan large applications. Additionally, the scanner lacks a GUI interface and does not possess a PDF report generation feature, as it is specifically designed for personal use.
Features of Grabber:
- File verification backup
- Ajax Verification
Conclusion
This article has seen what security testing is, why we need it, different types of security testing, and tools used to perform the testing and features. This article will help you choose testing tools based on your requirements and the features given above.
Recommended Articles
This is a guide to Security Testing. Here we discuss the introduction, types, methodologies, and top 10 open-source security testing tools. You can also go through our other suggested articles to learn more –