Updated March 23, 2023

Introduction to Penetration Testing Services
Other names of Penetration testing services are pen testing or ethical hacking. The cyber test that is authorized to perform security checks on the system is called penetration testing. Full assessment, including the weakness and strengths of the system, is evaluated using this test. By the 1960s, computer systems’ security became a concern as they were made to communicate and interact between systems. The first conference regarding computer security was done in June 1965. Teams were formed to understand system weaknesses in 1970, and the teams were called tiger teams. Free and commercial software is available to do penetration testing.
What is Penetration Testing?
This is the description of penetration testing, which is in detail given below:
- The vulnerabilities of the system are tested so that the testers will know the ways the attacker may exploit the system. Also, the system’s strengths are made known, which helps to make the system appear stronger than usual.
- The testing is either automated or manual. Automated testing is carried out with other software applications.
- Information about the target is gathered before the test, and the entry points of the attacker are identified. A report is created with all the details, including the break-in attempts, and given to the system supervisor.
- The weakness of the system is identified using this testing. The organization’s approach to security is a major concern in this test. Also, the system compliances with different policies, security policies of the system employee’s take on the security, and the organization’s response after the security threats are noted and reported to the administrator.
- The information report is passed to the network managers and IT administrators so that they can make decisions and remedial measures to manage the system security.
- Since this is an ethical hacking process, the testing is also called white hat attacks.
- The company’s security policies are well analyzed during this testing. If there is any loophole in the policy, the hacker notices the same and alerts the administrator.
- Based on the reports, the administration can take steps to analyze the system and make investments for enterprise systems’ security.
- Developers are made to create more powerful applications after knowing the weaknesses. The application loopholes’ errors can be avoided if the developers are notified about the way the hackers entered the application.
- It is important to do penetration testing whenever a new application is introduced in the enterprise, or the existing applications are modified. Also, when the policies are upgraded, or new offices are established, it is mandatory to do the testing. Even if no changes happen, it is mandatory to do pen testing once a year.
- Larger companies are more vulnerable to attacks. Hence the administration should be open for penetration testing. Also, since pen testing is costly, smaller companies may not be able to afford the cost of testing. The only way out is to build strong applications and do routine checks for security attacks.
Top Companies that Provide Penetration Testing Services
Since penetration testing appears costly, it is better to have a check and call around before deciding the companies.
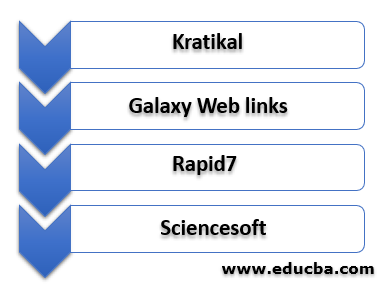
Here are a few companies for testing.
- Kratikal: Tools are provided to protect the company from cyber-attacks.
- Galaxy Web Links: The best company to do penetration testing and give quality assessments.
- Rapid7: Automation testing is done, and visibility is provided.
- Sciencesoft: Along with security checks, software development is also carried out in the company.
Other companies include senla, clavax technologies, testhouse, NesIdeology, and many others. Do a bid for the companies providing security measures and do the testing.
Advantages of Penetration Testing Services
Given below are the advantages of penetration testing services:
- The obvious advantage is to protect the system from threats and unknown vulnerabilities.
- Since penetration testing does the routine checks of compliance, monitoring is also done. This helps the companies to get away from penalties and other fines.
- Testing parameters are checked, and if there are any unknown parameters to the company, they are made known about the same.
- Due to penetration testing, the organizations will get to know the security threats and strengths that make them strong enough to face hackers.
- If an attack happens, heavy loss incurs in the company due to network downtime and employee work time. These losses are avoided if penetration testing is carried out in a routine manner.
- Due to vulnerability attacks, several data loss happens. The company image is spoilt, and customer trust is lost. These losses will not happen if the checks are carried out.
- Prevention is better than cure. Once the attack happens, it takes time and money to get the company back to its original shape. Since the testing exposes the vulnerabilities, it is advantageous to do the checking.
- The company’s defense mechanism is tested during penetration testing. This helps the company see it from a different perspective and make the developers build strong applications. Employees are made aware of the same.
- The business is not interrupted due to penetration testing, and it is done to avoid any interruptions in the future. The concerns regarding the risks exposed and vulnerabilities help the company to improve itself and make a strong name.
- The report provided by the penetration tester helps the administration to make good decisions about the weakness. The opinions from third parties are never neglected as they have done the hacking already.
- Client-side attacks are prevented due to penetration testing. Client-side attacks prove to be costly as there will be a business loss for the company. Also, trust is lost once the attack proves to be successful.
Conclusion
Since the attacks happen via the internet, it is mandatory to do the checking whenever the network infrastructure changes. Experts should do the testing, and all the facilities should be provided. Trust of the customer is important, and hence this should not be kept in check. Various tools should be analyzed while doing testing.
Recommended Articles
This is a guide to Penetration Testing Services. Here we discuss penetration testing services and the companies that provide these services and their advantages. You may also look at the following articles to learn more-