Updated November 7, 2023

Data Security Techniques
If the internet and information technology have simplified our lives, it has also given birth to several security-based threats. Therefore, protecting your crucial data and other information with appropriate data security techniques and data privacy has become equally important. However, your first task is identifying the confidential data you want to protect from leaking. This identification can only be made after you have carefully completed the auditing. Once you have understood the meaning of data security, your next job is to get a methodical understanding of which portions of your data are vulnerable and need definite protection.
The hackers, the phishers, and the pharmers have become quite smart these days, so you need to be smarter than them to nullify any risk factors. Data security techniques highlight all the vital steps that need to be taken to keep your information secure and intact. However, it is important to remember at this juncture that not all steps may be applicable and relevant to every company.
Top 8 Important Examples Of Data Security (Types)
Let’s Get started with The 8 Important Examples Of Data Security Techniques and Privacy:
#1. Data Security Techniques – Installation of Antivirus Software
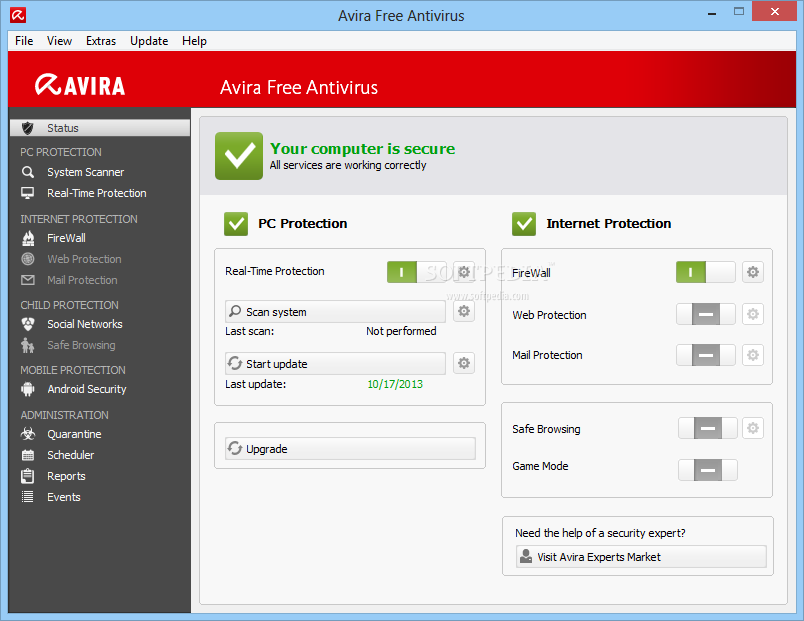
After you understand the data security meaning, let’s start with various viruses and malware threats that keep attacking the computer system. Hence, it becomes essential that every computer system has updated antivirus software installed on it, and it’s one of the best data security examples. The mere software installation will not solve your purpose, but you must update it regularly, at least a week. You must know about configuring the software. However, it is also pivotal for you to know about the different kinds of viruses.
Of course, they are unwelcomed guests penetrating your computer through various sources such as external hard disks, including infected pen drives, CDs or DVDs, browsing of unprotected websites, emails, and other files and documents. Some viruses can be easily detected and removed with antivirus software, while others are hidden, making tracing difficult. Other than viruses, the computer can also be affected.
- Trojan Horses
A Greek letter can bring malicious code that can adversely impact essential files and software if it penetrates your computer. Trojan horses attack the system when you are downloading something from an unknown and unprotected source. Thus, you must check the website’s authenticity before downloading a file.
- Worms
Security experts say the worms pose an even more significant threat than the virus and can quickly enter your system. They usually attack through fraudulent emails or fake websites, infecting files and documents. They spread more rapidly and attacked the bulk system at one time.
#2. Installation of Latest Updates to Purge Data Security Techniques Threats
It was found through a study that most Microsoft software, such as the operating system like Windows XP, has highly sensitive codes. These codes may likely have some difficult errors at times, but this is also one of the best data security examples. These errors mainly include the improper function of the codes, program lockups, and so on. They tend to weaken security, which the hackers quickly take advantage of. They can access protected files and often damage the data through illegal methods.
However, it is not that such issues cannot be addressed. You can make use of updates and patches by downloading them for free. They are also referred to as the service packs. It would help if you kept an eye on the program updates. It is better not to use old versions of the Microsoft operating system or MS Office like 1998, 2001, 2003, XP, 0W’ord doc, Powerpoint, Excel, Outl, etc.
#3. Data Security Techniques – Do not Use Spyware and Adware
As a computer owner, you must be vigilant about the threats of viruses and worms penetrating the computer stand and other evil and dangerous hazards for your confidential files and documents. It is better to browse or surf the internet all alone. See that nobody is spying on browsing habits and gathering sensitive information from your computer. But before that, you should know what adware is.
- Adware
Adware is usually spying software using which a person can get to know what kind of web pages you visit on the internet. You might have encountered pop-up ads that appear in a different window while browsing the internet. You need to immobilize some parts of JavaScript and ActiveX controls to eliminate such unnecessary. However, there are a few exceptions to fake adware. This largely depends on the software’s authenticity and its licensing agreements.
- Spyware
On the other hand, Spyware is like unwanted bugs that infringe on your computer on its own. They are Trojan horses or an illegal file that automatically gets downloaded even when you do not want it. It spices your info and computer activities, recording them all on a hard drive without your knowledge. This makes the job easier for hackers as they can easily detect confidential information such as passwords, bank details, ATM card pins, etc.
#4. Data Security Techniques – Always Choose Unusual and Tricky Password
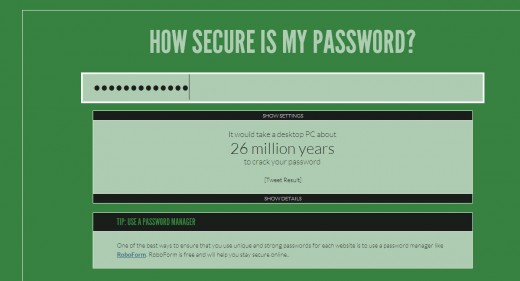
Many times you must have read that hackers were able to hack an email account or a website because they could easily crack down the password. A password is an essential tool that keeps all your information safe and secure. It is advisable to choose a password that has good strength in terms of characters. You might complain that complicated passwords are difficult to memorize, and people often tend to forget them. But you can note it down somewhere. The following necessary steps must be ensured to keep your password secured-
- Always write down your password in a safe and secure place and not on computer monitor screens where it can be easily accessed.
- When signing into your account (email, Facebook, or Twitter), the administrator usually offers you two options; Remember the Password and Nope. Never choose the first option. By doing so, anybody operating your computer can view your password.
- Don’t disclose your password to anyone, not even your closest friend or relative whom you trust entirely.
- It would help if you kept changing your password for a duration of every few months. Never keep one password for any account for too long.
- Try to maintain different passwords for different accounts. For instance, the password of your email id should not match with Facebook or vice-versa. Suppose you have two email IDs; the password should never be identical.
#5. Data Security Techniques – Creating a Strong Password
A strong password is also in the list of data security examples because you know the necessity of creating a full, strong password that does not easily fall on the hackers’ radar. The attackers usually use password-cracking tools such as intelligent guessing, automation, and the attacks’ dictionary.
Some Essential Features of a Strong Password
- An ideal length of any password is not less than eight characters.
- It should always include a character typed in upper or lower case, special characters such as (@,#, $), also known as symbols, and at least one number from one to zero. It is ideal for putting symbols in the second or sixth position.
- Please make these as your passwords; your name, user ID, date of birth, the locality where you live, the name of your parents, school or institution name, your vehicle number, mobile number, or any extremely easy word.
#6. Data Security Techniques – Try to Avoid the Endangers of Emails
We often assume that email is one of the most important and effective means of electronic communication today. It’s absolutely correct. However, one must also view the other side of the coin. You will be in trouble if you are not alert and vigilant on your email account. Cyber experts believe that emails are the easiest and quickest methods probably employed by attackers to send viruses into the bulk of computer systems in an office. Here are the steps to ensure email security and privacy.
- Password Protected Emails
A password protects nearly every email id; you must sign in by typing your username and password. Nobody can use your email account for any purpose without knowing the password.
- Check everything before pressing Send.
It is extremely easy to send mail to anybody with just a click on the Send button. However, it would help if you were very careful before emailing anybody. You should ensure you have entered the receiver’s correct and full email address. As a company owner, you are responsible for teaching your employees how to protect confidential information.
- Maintain the Privacy Statements
Most of the large companies have a privacy statement that is included in their emails. You will mostly find it towards the end of the mail, probably in the form of signature text. If you ask an expert, he would certainly say that it is a great tool to have in your asset.
- Do not get under Phishing Attack.
These are the common tricks hackers or phishers use to trap victims through fake or hoax email IDs to know sensitive information such as bank details and other financial info. They often use company logos and email IDs of reputed and large companies to target their victims. The email will appear fully authentic, but it is just illegal mail. They try to entice people through huge cash prizes and other rewards. Please be very careful and do not answer back to any such emails. Delete them immediately.
- Use of Email Encryption
This is yet another effective and valuable way of protecting your emails from hackers, especially if the message’s content is exceedingly confidential; it becomes quite difficult for anybody to decode the content in such a scenario because it is in an unencrypted format.
- Make Use of Spam Filters
Spam is the unnecessary or unwanted emails that enter your inbox whenever you clean them. However, using spam filters, you can eliminate unsolicited emails, as they will not allow them to come to your inbox. You know that most spam is fake emails irrelevant to your work. They can be intentionally loaded with the virus to disrupt the computer system.
#7. Data Security Techniques – The Usefulness of Installing a Firewall
Installing a firewall is also one of the data security examples because when you are using the internet, the connection established is from both sides. However, you may unknowingly encounter some unauthorized web pages while accessing the internet. Thus, it would help to have a strong security tool to prevent such an instance. Practically speaking, the firewall always plays the all-important role of a guard protecting your system against visiting fake websites. It will keep an eye on all the ports and warn you as soon as you enter the unprotected territory of a website.
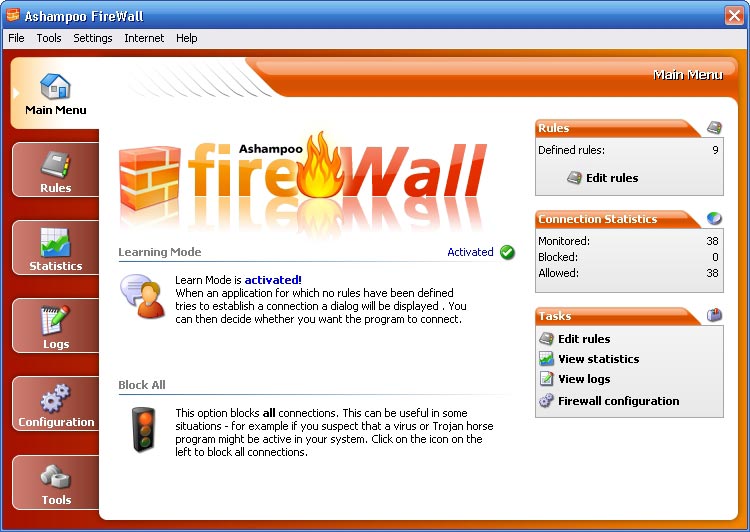
You can install the important firewall in hardware or data security techniques software. Talking about the installation process, software firewalls are always easier to install. You can only use these for one computer system. On the other hand, hardware firewalls protect an entire computer system network. Whichever internet connection you use, installing a firewall for your personal system in the office is essential.
#8. Data Security Techniques – Locking your All Important Files & Documents
In Data security examples, locking your files and documents is also a useful example of data security techniques because electronic data can be accessed anywhere. Suppose you do not want everyone to access all your documents, lockdown, and protect your data wherever it is. However, it would help if you remembered the place where you had secured your data. Apart from that, it is essential to protect your servers as well.
Conclusion
The data and other vital information stored in the computer system are quite sensitive and confidential for you and your company. With large cyber threats, ensuring robust and fortified security data and privacy has become crucial. In addition to following the steps, you should always remain alert and attentive while using the internet.
Recommended Articles
This has been a guide to IT and has given birth to several security-based threats. Here are 8 essential ways to ensure complete data security techniques and privacy. These are the following external links related to data security techniques.


