Updated August 10, 2023
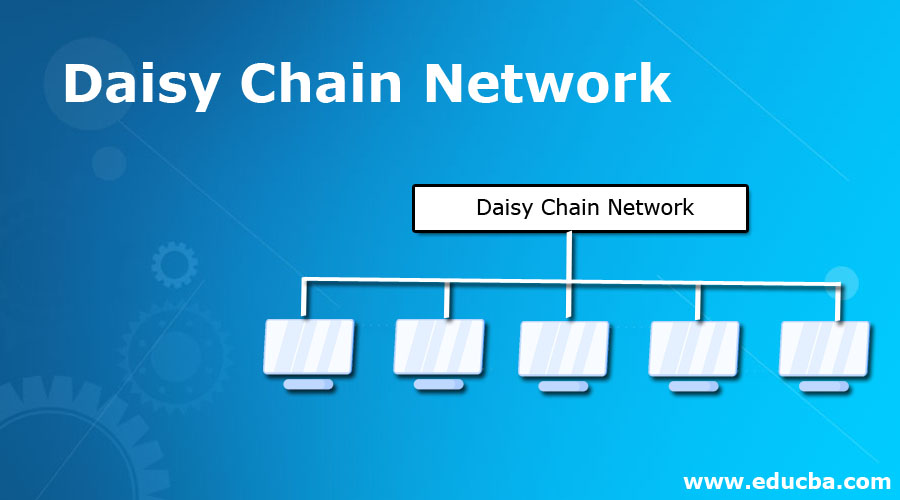
Introduction to Daisy Chain Network
A daisy chain network is a wiring schema, where multiple devices are linked together in a typical sequence or structure of the ring. It is similar to the daisy flower garland. Apart from full loops, the single loop system comprises of multiple internal loops but cannot be said as daisy chains. Mostly the daisy chains are used for power systems, analog signals, digital information, and rare combination of all. The word daisy system signifies about large scale devices associated with series like power strips that are plugged into each other to forma unit long line or to the embedded wiring sequence inside of the device. Other few examples are the daisy chain network is based on the USB, Ethernet, FireWire, and thunderbolt.
What is the Daisy Chain Network?
A daisy chain is used to direct the connection of network nodes and nodes of the computer. It is a typical type of network topology. Varied topology supports objectives, persistent, fault-tolerant and user-friendly. It is also simple to implement. One node of the network is connected to the next in line or chain. It can be linear where the initial and last nodes aren’t linked and it can also be formed as a ring by connecting the initial and last nodes. The ring topology enables bidirectional passing whereas, in linear, the message must flow from one system to another in a single direction. It is low adaptable but it resembles like electric series circuit where a fault in one system affects the other linked components. A well-built network can isolate the faulty sections without disturbing the process of other systems. In a ring structure, the transportation of data is made in both directions. So if any faulty node occurs, it cut off the concerned parts from the rest of the network.
Other network topologies include a hub as a central system to pass the message from other nodes. Star topology is capable to handle multiple outages of nodes without disconnecting the working machines.
Why do we Use the Daisy Chain Network?
Some hardware can be connected to a computing system in a daisy chain network by associating each component to another similar component, instead of directly connecting to the computing system that uses the component. Only the final component in a chain connects directly to the computing system. For instance, linking many components with UART ports to each other. The components must be connected properly to behave in coordination. Only one component seizes the bus at one time only.
SCSI is electrically a bus which is an example of a digital system, it is similar to the external devices which are wired as similar to the daisy chain which has high scalability. Because the system is electrically a bus, it should be terminated and this is possible by plugging a terminator into the final component or choosing an option to make the component terminate internally. MDI components are generally designed to be wired in the daisy chain. It is common for a component to have both OUT and THRU port and often they are used for linking. The THRU port transports the data with minimum delay and no changes when the OUT port transmits a complete regenerated signal. It may add, change or remove the message in case of any ongoing delay. The difference reflects in the signals arriving at different time sequences. If the chain is long, there is a possibility of distortion which results in undependable and non-functional systems. But few SPI IC components are configured with daisy chain ability. All integrated circuits, JTAG supports the daisy chain concerning its JTAG daisy chain guidelines. Thunderbolt is an interfacing component that supports daisy chain devices like computer monitors and RAID arrays. The Hexbus is Texas instruments used in TI-74 is made of the 10-wire bus.
The user can combine the sessions of daisy chain computing by Telnet or SSH. The user builds a session on the second computer by Telnet and from that session, Telnet to a third computer and goes on. It is said as the terminal session within another terminal session with the help of RDP. The focus of daisy chain creation is to includes connecting to a server on a non-routed network through gateway networks, preventing sessions on a first computer when working on the next computer to preserve the bandwidth or to enhance the connectivity on an unbalanced network by connecting it to a better stable machine. The overall focus is on masking the activity when engaged in cybercrime functions.
The daisy chain network is well known for its simplicity and scalability. The user can add extra nodes along the chain up to a maximum extent. A daisy chain network can have a long-distance from one end to another but it is not suitable in all circumstances where nodes must be distributed all over the geographic area. In that case, the cable is zig-zag around and the entire length of the network can become large when comparing to the actual distance between the nodes. It can cause the network to slowly operate for users who are near to opposite ends of the chain. Daisy chain has the term of a newly built virus hoax.
Types of Daisy Chain Network
The daisy chain network is developed in any one of these network topologies, linear or ring topology
- The linear topology of the daisy chain network is the two points such as initial and final points of the network is not connected at their ends or together. It provides a unidirectional flow of data.
- Ring topology of the daisy chain network is the initial and final points of the network are connected and formed as a ring. It is frequently called a daisy chain loop. The flow of data in this system is bidirectional.
Conclusion
The ring daisy chain system has more benefits than a linear daisy network because of the two-way links. In the case of ring breakage, then transmission happens in the reversible path by checking the connectivity. Hence it is applied in the Metropolitan Area Network.
Recommended Articles
This is a guide to Daisy Chain Network. Here we discuss the Introduction and What is a Daisy Chain Network and we also discuss why we use along with its types. You can also go through our other suggested articles to learn more –


