Updated March 17, 2023
Introduction To Asymmetric Encryption
Asymmetric cryptography, which can also be called public-key cryptography, uses private and public keys to encrypt and decrypt the data. The keys are simply large numbers that are paired together; however, they are asymmetric means not identical. Public Key is One of the keys in the pair that can be shared with everyone, whereas Private key is the other key in the pair that is kept secret; it is called the private key. Any key can be used to encrypt a message then the other key, which is not used for encryption, is used for decryption.
What is Asymmetric Encryption?
Encryption is the method of converting the data into a cipher format using a key. The encrypted data can be safely shared with others. It will be difficult to break the cipher format if the algorithm/key used is strong and properly implemented. The receiver deciphers the data to the original format using the key used earlier to encrypt it.
The above method is followed in symmetric encryption, where the ciphered data and the key are sent to the receiver for consumption post decryption. Challenges in this mode are the manageability of many participants and exchanging a key in a secure way.
Asymmetric Encryption robustly addresses these challenges with a pair of keys: a public key and a private key. While the data is encrypted at the sender’s end using the receiver’s public key and the data exchanged is decrypted by the receiver using his private key. Though the public key is made available to everyone, a private key that is essential to decrypt the data is retained with the owner.
Difference between Symmetric and Asymmetric encryption
| Symmetric | Asymmetric |
| Uses One key for encryption and decryption. | Uses two keys, one for encryption and the other for decryption. |
| Encrypted data and keys are exchanged. | Only the encrypted data is exchanged, and the public key is available for anyone. |
| Quicker | Slow |
| Unmanageable if no of the participants become higher. | Operations can be streamlined with pairs of public and private keys. |
| Risk in exchanging the key in the network channel. | A private key is not exchanged. |
How does Asymmetric Encryption work?
A public key and Private keys are generated randomly using an algorithm, and the keys have a mathematical relationship with each other. The key should be longer in length (128 bits, 256 bits) to make it stronger and make it impossible to break the key even if the other paired key is known. The number of possible keys increases proportionally with the key length, and hence cracking it also becomes tougher.
The data is encrypted using any one of the keys and decrypted with the other. The algorithm used in asymmetric encryption are:
| Name | Description |
| Diffie-Hellman Key Agreement | Sharing key for exchange of information confidently. |
| RSA (Rivest Shamir Adleman) | Encryption and Digital Signature |
| ECC (Elliptic Curve Cryptography) | Functions are similar to RSA, and it caters to cell devices. |
| El Gamel | Digital Signatures and keys are exchanged through this logic. |
| DSA (Digital Signature Algorithm) | Used only in digital signing. |
Scenarios
Let us analyze a hypothetical scenario to understand how Asymmetric encryption works.
Sales agents from various regions will have to send sales data to head office during month-end in a secure way to keep the information out of competitors’ reach.
The head office will generate private/public keys for each agent and communicate the agents’ public key. An agent will use the public key in encrypting the sales data and send it to HO. HO will decipher it using the agent’s private key and get the data in the original form. The entire information exchange had taken place in a secured manner, and even if a public key is leaked, the secrecy is not lost because the only private key is used to decipher, and it is safely lying in HO.
Another scenario is in the https site of a bank where payment is involved. A client gets the public key from the bank web site and sends passwords and other confidential details to Bank after encrypting it with a public key, and the Bank deciphers the details with a private key of the client.
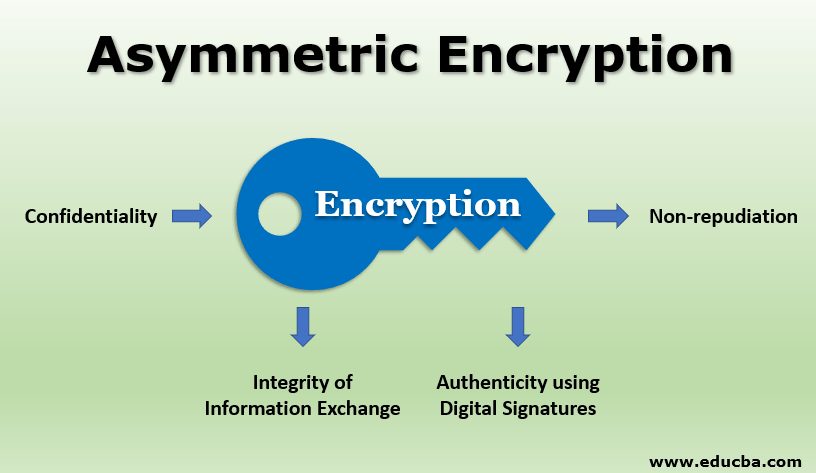
Applications of Asymmetric Encryption
Below are the different applications of Asymmetric Encryption:
1. Confidentiality
The most common application of Asymmetric Encryption is confidentiality. This is achieved by sending critical information by encrypting it with the receiver’s public key and decrypting it with its own private key.
2. Authenticity using Digital Signatures
A sender attaches his private key to the message as a digital signature and exchanges it with the receiver. The receiver uses the sender’s public key and verifies whether the private key sent belongs to the sender, hence ascertaining the sender’s authenticity.
3. Integrity of Information Exchange
One way the hash of the data to be exchanged is created and encrypted using the sender’s private key. Encrypted hash and data are exchanged with the receiver. Using the sender’s public key, the receiver decrypts the hash and recreates the hash. Any difference between the two hashes indicates the content is altered after signature and integrity are lost. This kind of integrity check is followed in digital cash and bitcoin transactions.
4. Non-repudiation
With the digital signature encryption tool in place, the owner of a document or information who exchanged it with others cannot disown the content, and a transaction done online cannot be disowned by its originator.
Advantages of Asymmetric Encryption
Asymmetric encryption provides a platform for securely exchanging information without having to share private keys. Non-repudiation, Authentication using Digital signatures, and Integrity are the other unique features offered by this encryption.
This method also overcomes the lacuna of Symmetric encryption (the need to exchange the secret key used for encryption/decryption) by exchanging the key alone through public key/private key in an asymmetric way and still exchanging high volume data using symmetric mode.
Conclusion
Asymmetric encryption provides a secured platform to exchange sensitive information, and it will help in accelerating e-commerce growth and adding a new dimension to digital initiatives.
Recommended Articles
This is a guide to Asymmetric Encryption. Here we discuss asymmetric encryption, how it works, the applications, and the advantages of asymmetric encryption. You may also look at the following articles to learn more –