Updated March 14, 2023
Overview of Cryptography Techniques
Various cryptography techniques have been developed to provide data security to ensure that the data transferred between communication parties is confidential, not modified by an unauthorized party, to prevent hackers from accessing and using their information. Caesar cipher, monoalphabetic cipher, homophonic substitution cipher, Polyalphabetic Cipher, Playfair cipher, rail fence, One-time pad, hill cipher are some of the examples of cryptography techniques.
Cryptography deals with various security principles, which are as follows:
- Confidentiality – It specifies that only the sender and the recipient or recipients should be able to access the message. Confidentiality will get lost if an authorized person can access a message.
- Authentication – It identifies a user or a computer system so that it can be trusted.
- Integrity – It checks that a message’s contents must not be altered during its transmission from the sender to the recipient.
- Non-repudiation – It specifies that the sender of a message cannot be refused having sent it, later on, in the case of a dispute.
Top 5 Cryptography Techniques
Here are some very easy codes and more complex modern encryption technologies used on the Internet today.
1) Simple Codes
- This category is any way of writing a message by side that it is difficult for anyone else to read. That involves writing stuff in another alphabet. Here we can see that Icelandic runes and IPA and another niche built alphabets such as the Deseret Alphabet.
- In this, we can use language to code. We have looked into the creation of created languages such as Elvish and Esperanto.
- Chester Naz and Judith Schiess Avila’s book Code Talker is a book that explains how the Navajo language had been used as a code in the Second World War and never was cracked into extremely intense conditions.
- If Navajo had no words for a particular notion, the code speakers chose a term instead. The Navajo word for ‘ hummingbird, ‘ for example, had become a fighter plane, and ‘ iron hat ‘ was Germany.
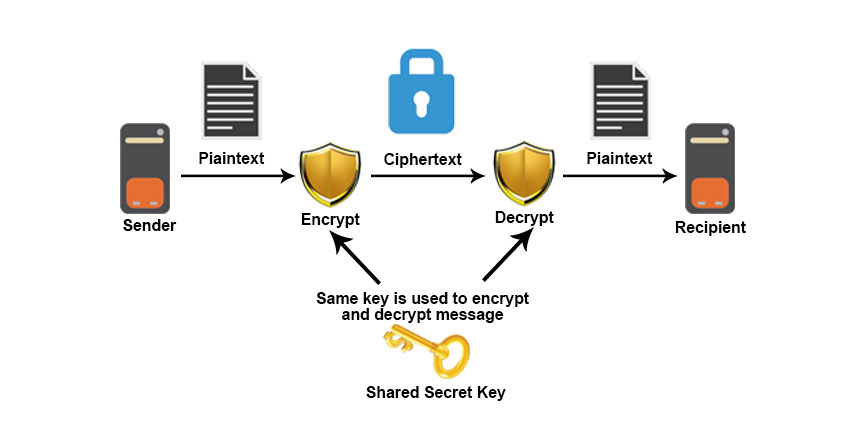
2) Symmetric Encryption
- Symmetrical encryption is a type of encryption that is used for the encryption and decryption of electronic data by just one key (a secret key). Substitution ciphers are symmetrical encryption techniques, but modern symmetric encryption can be much more complicated.
- Data are converted to a method that anyone cannot understand without a secret key to decrypt it using symmetrical encryption algorithms.
- Symmetric encryption is an old algorithm, but it is faster and efficient than asymmetric encryption. Because of great performance and fast speed of symmetric as compare to asymmetric encryption.
- Whereas Symmetric key cryptography involves the usage of the same key for encryption and decryption. At the same time, Asymmetric key cryptography involves using one key for encryption and another different key for decryption.
- Symmetric encryption is typical for big quantities of information, e.g. for database encryption, in bulk encryption. In the case of a database, the secret key can only be encrypted or decrypted by the database itself.
We can see the working of Symmetric encryption in the picture given below:
Two kinds of symmetrical encryption algorithms are available:
- Block algorithm
- Stream algorithm
A) Block Algorithm
The set of bits is encoded with a specific secret key in electronic data blocks. The system keeps the data in its memory while it is waiting to get complete blocks when the data are encrypted. Some important Block cipher algorithms are DES, Triple DES, AES, etc.
B) Stream Cipher Algorithm
In this, Plain text numbers or characters are combined with pseudorandom cipher digit stream. Some important Stream cipher algorithms are RC4, A5, BLOWFISH, etc. In symmetric key encryption, The encryption code can be cracked if someone finds out the symmetric key. But this problem can be overcome with the Diffie-Hellman algorithm. In the Diffie-Hellman key exchange or agreement algorithm, the sender and receiver must agree on a symmetric key using this technique. This key can then be used for encryption or decryption purpose.
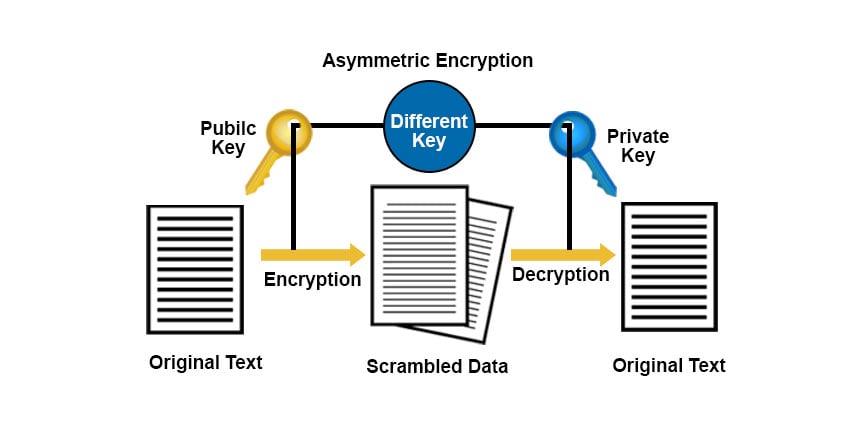
3) Asymmetric Encryption
- Asymmetric encryption is also called public-key cryptography. Asymmetric key encryption helps to resolve a key exchange problem of symmetric key Cryptography. In Asymmetric encryption, Two keys are used to encrypt plain text in asymmetrical encryption. Through the internet or big network, the secret keys are exchanged. It is necessary to notice that anyone with a secret key can decrypt the message, so asymmetric encryption uses two corresponding keys to increase safety.
- Anyone who wishes to send you a message will have a public key freely accessible, but the second private key is held the secret for you to understand you only. A message encrypted with a public key can be decoded with a private key. A message encrypted with a private key can also be decrypted with a public key.
We can see the working of Asymmetric encryption in the picture given below:
4) Steganography
- Steganography is a technique that facilitates the hiring of a message that is to be kept secret inside other messages. Earlier, people used methods to hide messages such as invisible ink, minute variations, etc.
- But in an age of technology, Steganography is a technique to conceal data that can be the file, message, image, etc., inside other files, message or images.
5) Hashing
- Hashing is the cryptographic technique that converts data that can be any form into a unique string. Regardless of size or type, any data can be hashed using a hashing algorithm. It takes data of random length and converts it into a fixed hashed value.
- Hashing is different from other encryption methods because, in hashing, encryption cannot be reversed; that is cannot be decrypted using keys. MD5, SHA1, SHA 256 are the widely used hashing algorithms.
Conclusion
This article has seen what cryptography and various Cryptography techniques to encrypt and decrypt the data are. Cryptography is used in all fields to secure data and prevent it from getting hacked. For example, for securing passwords, authenticating banking transactions, etc. Nowadays, various new cryptographic techniques are developed and cracked; hence, it is important always to be aware of computer threats and take precautions to avoid them as best as we can.
Recommended Articles
This is a guide to Cryptography Techniques. Here we discuss the basic concept with few techniques of cryptography respectively in detail. You can also go through our other suggested articles to learn more –