Updated May 22, 2023
Overview of the OSI Model
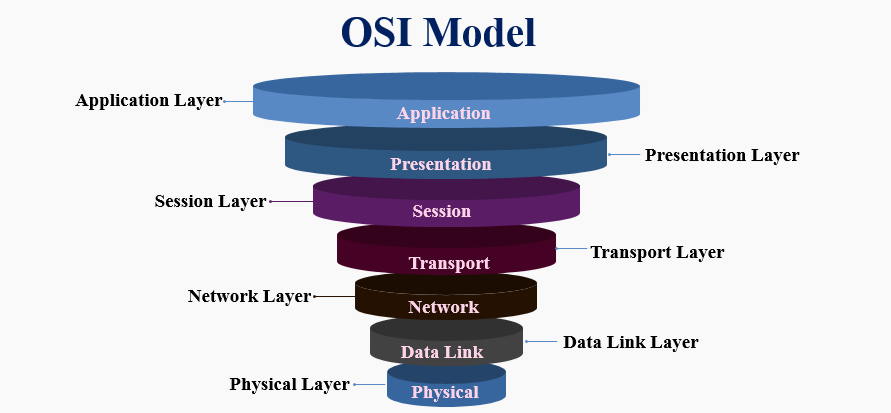
OSI model stands for Open System Interconnection mode, developed by the international organization for Standardization in 1984, designed to show the flow of moving data from one software application of one computer to another. It consists of seven layers – Physical layer, Data link layer, Network layer, Transport layer, Session layer, Presentation layer, and Application layer. Each layer has its tasks, which are performed independently.
What is OSI Model?
OSI Model is a network model having seven different layers. This model was first introduced in 1974 by the ISO (International Organization of Standardization). This model helps to transfer data over the network from one computer device to another. This model is nothing but the standard adopted all over the globe.
- OSI Model Definition: the Open Systems Interconnection (OSI) model is the virtual model that describes the Concept of a computer system with internal structure and technology.
- Understanding the OSI Model: The Open Systems Interconnection (OSI) model is divided into seven layers, as shown in the below diagram:

7 Layers of the OSI Model
As you can see in the following diagram.
There are two computers. These two computers are trying to communicate with each other over the network. Physical, data link and network layers are the hardware layers of this model, and Session, presentation, and application are the software layers of the model. The transport layer is the Heart of the OSI Model.

Working with the OSI Model
Let’s see what exactly these all:
- Physical Layer: The Physical layer is the first layer of the OSI Model. The physical layer works to send individual bits from one node to another. This layer is responsible for the connection between two devices. Whatever data comes to this layer is converted in binary format, i.e., 0’s and 1’s. After converting it, send data to the Data-link layer.
- Data Link Layer: The Data Link layer is the second layer above the model’s Physical layer. The data link layer is responsible for moving frames from one node to the other. This layer makes sure that data received or transferred should be error-free. It also ensures security by attaching some bits at the start and end of the frame.
- Network Layer: The Network layer is the third layer of this model. The network layer must deliver the packets from the source node to the destination node. It sends data from one network to another. It makes use of different routing algorithms to send data. The network layer carries an IP address at the header.
- Transport Layer: The Transport layer is the fourth layer of this model. The transport layer delivers the message from one process to another. It takes data from the network layer and transmits data to the application layer. In this layer, the main thing is acknowledgment. Acknowledgment is the process of data transmission over the network successfully. This layer resides on the operating system of the device. It works with the system calls.
- Session Layer: The session layer is the fifth layer. As the name suggests, this layer manages sessions between end-user application processes.
- Presentation Layer: The presentation layer is the sixth layer. The Translation layer, or the Presentation layer, is responsible for presenting data to the application.
- Application Layer: The Application layer is the last and seventh layer of the OSI Model. This layer is the abstraction layer. Which handles sharing protocols over the computer network with OSI and TCP/IP
Advantages
- OSI model acts as a pathway to develop any network model.
- OSI is a 7 layered network model. All the layers work individually. They do not affect other layers.
- This model is very flexible.
- It supports both connection-oriented services and connectionless services.
- It guides network administrators in deciding the necessary hardware and software to build their network healthily.
- Helping hardware manufacturers create networking products that can communicate with each other over the network without defects.
- It helps to teach the working of a network to others.
- This model reduces complexity.
- It helps troubleshoot easily; As a network administrator, it helps recognize defects more quickly.
Why Should We Use the OSI Model?
In earlier days, when this model was introduced, there was a problem with connectivity. Some models already exist. But connecting with a different model regarding computers’ connectivity wasn’t easy. To solve this problem, one standard model got introduced, which is nothing but the OSI Model. Now each network device is getting created based on this model.
Need for the OSI Model
It is a key part of networking. All software and hardware devices follow the specifications mentioned in this model.
How will this Technology Help you in Career Growth?
If we see at the computer world, networking is never-ending technology. In computers, every aspect network plays a vital role. If you desire to make a career in computer networks, there is a never-ending demand for network administrators. Knowing this model thoroughly, you understand the overall networking concept. With this advantage, this work is also enjoyable. Every time we are working on this, something called real-time with networks.
Conclusion
OSI Model must be known to every computer engineer as it is an essential and mandatory technology to work with networks. Some theories also state that networking is the technology that comes with job security. So at the start of your career, it is good practice to know this model.
Recommended Articles
This has been a guide to the OSI Model. Here we discuss the 7 layers, working, advantages, need, and uses. You can also go through our other suggested articles to learn more –


