Updated July 5, 2023
What is Data Link Layer
The Data Link Layer is the second layer of the OSI model and lies between the physical layer and the network layer. OSI, or in other words, the Open Systems Interconnection model, is a conceptual model which is used vastly in the software industry, especially in the field of communication, for characterizing and standardizing the functions without touching the internal structure underlying the structure or technology. This layer in the OSI model defines the protocol for the establishment as well as the termination of a connection between two devices. This layer is subdivided into 2 sublayers, namely, Medium Access control and Logical Link Control. In the below few sections, we will look in detail at these 2 sublayers as well as other components.
Layers of the OSI Model
In the previous section, we already had a glimpse of what the OSI model is; now, let us see what the other layers in this conceptual model are. The 7 layers of the OSI model are:
- Physical Layer
- Data Link layer
- Network Layer
- Transport Layer
- Session Layer
- Presentation Layer
- Application Layer
Now looking into the sublayers of the data link layer, i.e. Medium Access Control (MAC) which helps in controlling the hardware responsible for interaction with the transmission mediums, and the Logical Link Control (LLC) which acts as a connection between the MAC sublayer and the network layer and uses a multiplexing mechanism for allowing several network protocols to coexist within a multipoint network. The division into sub-layer is to bring in the concept of modularity for standardized practice.
The main functionality of the Data link layer is the transfer of the datagram across an individual link. Now in this statement, we came across two new terminologies, and let us look briefly into those first before proceeding ahead. One of the terms is Link, and Link is the communication channel through which adjacent nodes are connected. For the other term, “Datagram,” let us understand it from an analogous situation. Now let us prepare an itinerary from Bangalore to some remote place in West Bengal. The entire travel will involve 3 basic transportation i.e. flights, trains, and a bus. Now, these three modes of transportation are independent of each other, and we assume the link to be direct in nature but perform a basic service of moving you from one location to its adjacent location so that you can take the next service. In this analogy, the one who is traveling is the datagram; each of the transportation segments the traveler is traveling is analogous to links, and each mode used is the link-layer protocol.
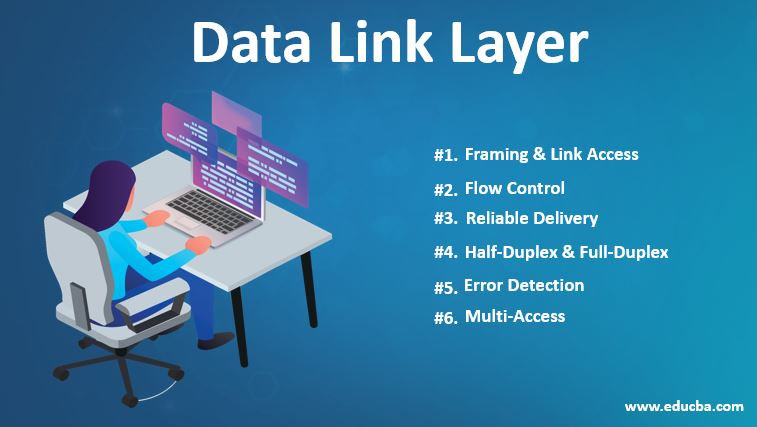
Services of Data Link Layer
Now we have a fair idea of what links and datagrams are and, at a higher level, what is a data link layer; let us look into the aspects and the services provided by them, which will encapsulate the importance of the data link layer in the OSI model. In a nutshell, we have 6 services that Data Link layer provides, and they are:
1. Framing & Link Access
Even before the transmission starts, the layer protocols encapsulate each network frame. Earlier, we discussed the frame, which consists of a number of data fields, and each data field comprising of datagrams inserted. The structure of the frame is specified here, along with the channel access protocol, which would be used for transmitting the frame over the link.
2. Flow Control
The stations through which the transmission happens might have different speeds or capacities, and this layer ensures that the flow of data works at the same speed for exchanging data. In case the flow is not controlled, the recipient buffer might overflow, leading to a loss of frames.
3. Reliable Delivery
Talking about transmission is incomplete without talking about reliable delivery service, and that is where the Data Link layer accomplishes that through the concept of transmissions and acknowledgments. Typically, we encounter the problem of flipped bits of a problem in the transmission. The errors are detected locally, and an attempt is taken to recover the original data along with the error reporting mechanism to the sender.
4. Half-Duplex & Full-Duplex
This characteristic of this is to provide flexibility in the transmission of data. In a full-duplex mode, both the nodes would be able to transmit data simultaneously, and in a half-duplex mode, only one node would be able to transmit data at the same time.
5. Error Detection
In error detection, Data Link Layers provide the functionality of providing a mechanism for detecting one or more errors that might have occurred by signal attenuation or noise. This detection functionality is possible by using error detection bits in the frame which is getting transmitted and, based on the bits, can perform an error check.
6. Multi-Access
The functionality of multi-access is of high importance as it avoids the collision which might occur due to the host on a shared link trying to share data. The mechanism of CSMA/CD is deployed for allowing access to shared media among multiple systems.
Advantages of Data Link layer
In the previous sections, we have holistically touched on different aspects of the Data Link Layer and dived deep into the importance of features it provides.
- Since the OSI model is very generic, having a standardized model helps in integration without much hassle.
- Having hidden protocols allows any protocol implementation and has the flexibility to adapt to many protocols.
- It provides a connection through connection-oriented methods as well as connectionless services. Connection services are used when we need high reliability, and speed is not of much concern, and vice versa requirement for connectionless transmission.
- Since there are so many functionalities around error detection and reliable delivery, the messages don’t arrive out of order.
Conclusion
In this article, we have had an overall deep dive into Data Link Layer, wherein we started by introducing what it is. In conclusion, it is responsible for the conversion of data streams into signals bit by bit, and at the end, the signals are picked and assembled into a recognizable frame format.
Recommended Articles
This is a guide to the Data Link Layer. Here we discuss the Services of the Data link layer and its important components and proceed to different features of the Data Link Layer. You may also have a look at the following articles to learn more –

