Updated March 14, 2023

What is the IDEA Algorithm?
IDEA (International Data Encryption Algorithm) is an encryption algorithm. It is a symmetric block cipher that takes 64 bit as an input, 28-bit key and performs 8 identical rounds for encryption in which 6 different subkeys are used, and four keys are used for output transformation.
Understanding IDEA Algorithm
- The typical block size is 16 bytes of 128 bits. A block cipher will typically operate in round blocks where part of the key is applied to the round, and then other operations are performed on it. After a certain number of rounds, say between 10 to 16, we end up with our ciphertext for that block.
- The ciphertext block is exactly the same size as the plain text block, 16 bytes. We operate on the block for each round using a part of the encryption key that we call as the round key. We derive the multiple round keys from the encryption key using a key schedule.
- The key schedule is an algorithm that Shifts, XORs, Multiplies and performs other types of operation on the original encryption key in order to come up with these round keys. Well, if I have a 16-byte block and I have a 128-bit key, which is also 16 bytes,
Confusion and Diffusion
Let’s understand the difference between Confusion and Diffusion.
Confusion
- Confusion has to do with the relation between key and ciphertext.
- We ensure that a small change in the key leads to a large change in the ciphertext.
- XOR is not sufficient; one-to-one.
- Key Schedule.
Diffusion
- Diffusion has to do with the relation between the message and ciphertext.
- A small change in the message -> large change in the ciphertext.
- Hides patterns within the message.
So Electronic Code Book mode of operation, we will usually run a block cipher in Cipher Block Chaining mode of operation or CBC. With cipher block chaining, you will XOR the previous block’s ciphertext with the previous block’s with the next block’s plain text before you were encrypted. In that way, every block in the message depends upon all of the blocks that came before.
Data Encryption Standard (DES)
Let’s look at some of the aspects of the Data Encryption Standard (DES).
Key Length
- 64-bit input
- 8-bit parity check
- 56-bit effective key
Weakness
- Theoretical
- Short key
Understanding IDEA Algorithm in Detail
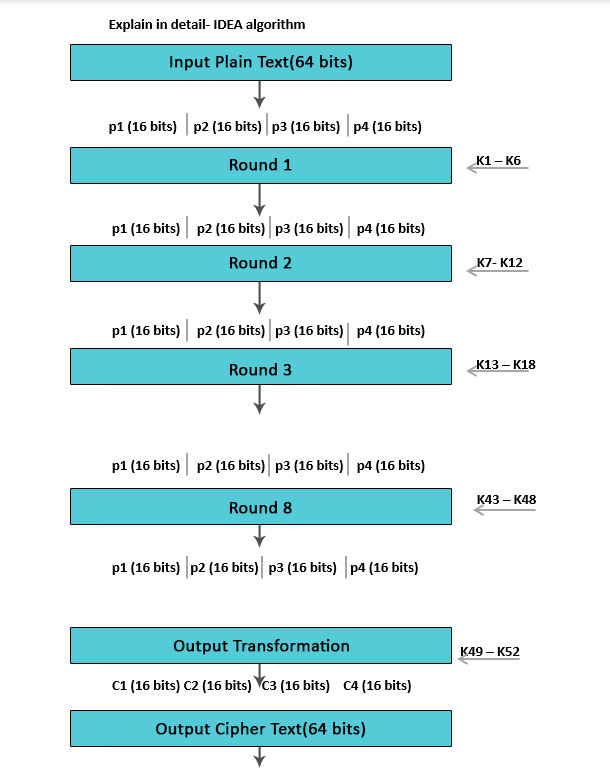
The 64-bit input plain text block-divided into 4 part (16 bits each) Declare p1 to p4.
- Therefore, p1 to p4 will be the inputs for the initial round of the algorithm.
- There are 8 such rounds.
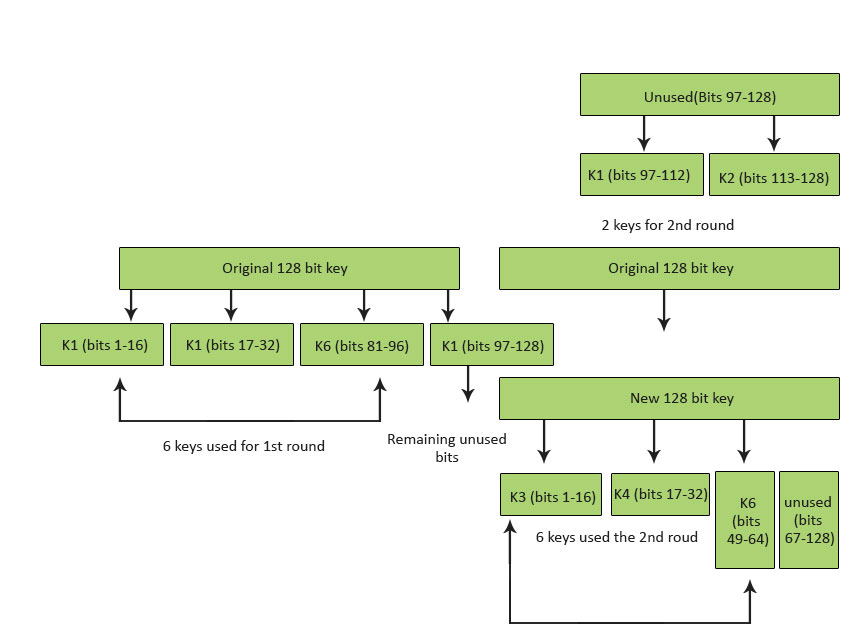
- The key is made up of 128 bits.
- In each round, 6 sub-keys will be produced.
- Each one of the sub-keys includes 16 bits.
- All these sub-keys will be put on the 4 input blocks p1 to p4.
- The last actions include Output Transformation, which usually benefits simply 4 sub-Keys.
- The last result is 4 blocks of ciphertext C1 to C4 (each of 16 bits).
- They are mixed to create the last 64-bit ciphertext block.
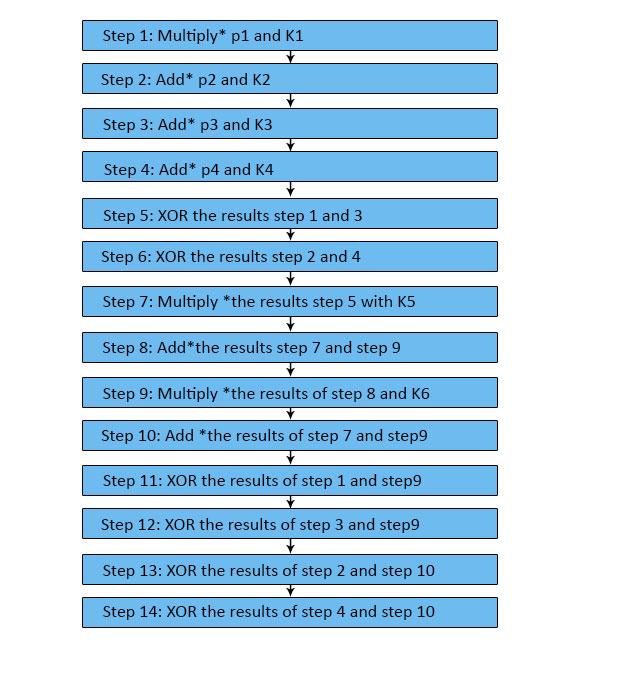
Single Round Information
- There are 8 rounds in IDEA.
- Every single requires several operations around the four data blocks applying 6 keys.
- These steps work in numerous mathematical activities.
- There are multiple *, add * & XOR procedures.
- Multiply * means multiplication modulo.
- Add* requires addition modulo.
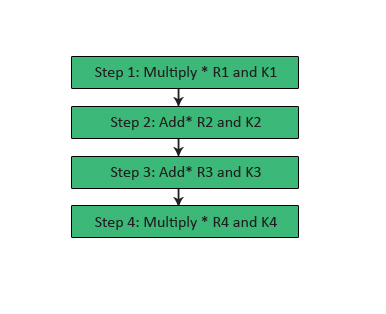
Output Transformation
- It can be a one-time procedure.
- It requires places by the end of the 8th round.
- The Output transformation input is a 64-bit value divided into 4 sub-blocks (state R1 to R4 every among 16 bits).
- The four 16 bits Sub-keys (K1 to K4) are used here.
- The process of the outcome transformation can be as follows.
Conclusion
- IDEA may be a recognized cipher that many experts have examined for the previous 10 Sub-key creation for the round, each one of the 8 rounds utilizes 6 sub-keys (hence 8 * 6 = 48 sub-keys are essential for the rounds). The last result transformation benefits 4 sub-keys (i.e. 48 + 4 = 52 sub-keys total). From an input key 128 bits, all these 52 sub-keys will be produced years, as well as; however, no strike against five or higher of its 8.5 rounds has been found.
- Because of its toughness against cryptanalytic attacks and because of its inclusion in several well-known cryptographic deals, IDEA can be trusted. The Basic IDEA algorithm is definitely not, which can be likened for effectiveness or security with simple DES or AES versions. The Basic IDEA algorithm is intended to assist learners in being familiar with the IDEA algorithm by giving a version of IDEA that enables instances to get worked well manually and to offer a comparison of the technique of IDEA and the ways of DES and AES.
Recommended Articles
This has been a guide to the IDEA Algorithm. Here we discussed the IDEA Algorithm’s understanding, data encryption standard, and the difference between confusion and diffusion of the IDEA algorithm. You can also go through our other suggested articles to learn more –