What is Cyber Security Compliance?
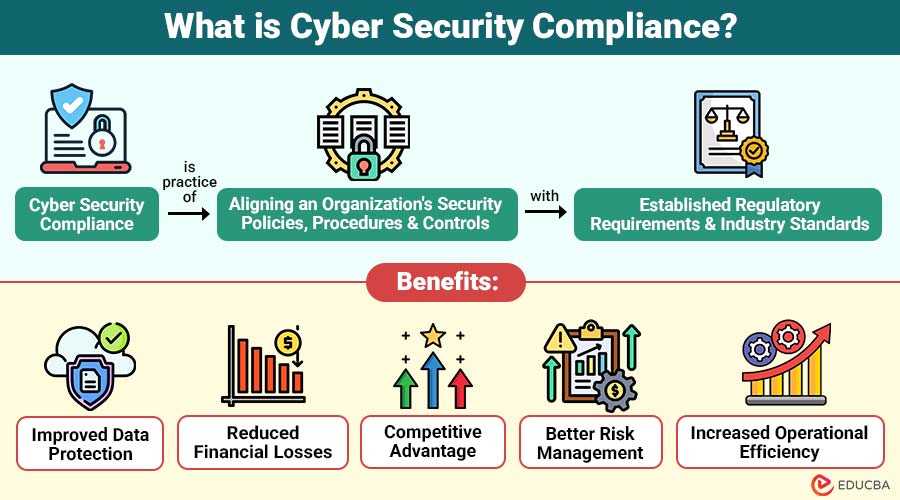
Cyber Security Compliance is the practice of aligning an organization’s security policies, procedures, and controls with established regulatory requirements and industry standards. These regulations aim to protect sensitive information, including personal data, financial records, and intellectual property.
Compliance requirements vary by industry, location, and the type of data handled. Organizations must regularly assess their systems, implement security controls, and demonstrate compliance through audits and documentation.
Table of Contents:
Key Takeaways:
- Cyber security compliance ensures adherence to data protection laws and standards.
- It helps organizations safeguard sensitive data and mitigate cyber risks.
- Compliance frameworks guide implementation of effective security controls and governance.
- Maintaining compliance requires routine monitoring and audits.
Importance of Cyber Security Compliance
Below are the reasons highlighting its importance:
1. Protects Sensitive Data
Organizations must implement safeguards such as encryption, access control, and monitoring to comply with compliance standards and protect data from unauthorized access.
2. Reduces Cybersecurity Risks
By following standardized security practices, organizations can minimize vulnerabilities and prevent data breaches, malware attacks, and insider threats.
3. Builds Customer Trust
Consumers are likely to trust companies that prioritize data protection and observe to establish security protocols.
4. Ensures Legal and Regulatory Adherence
Compliance helps organizations avoid legal consequences by meeting mandatory requirements set by governments and regulatory bodies.
5. Enhances Business Reputation
Organizations that maintain strong security compliance are perceived as reliable and responsible, enhancing their market reputation.
Major Cyber Security Compliance Frameworks
Different industries follow specific compliance frameworks. Some of the most widely recognized include the following:
1. GDPR (General Data Protection Regulation)
- Applies to organizations handling data of EU citizens
- Focuses on data privacy and user consent
- Requires strict data protection measures
2. HIPAA (Health Insurance Portability and Accountability Act)
- Applicable to healthcare organizations
- Protects patient health information
- Mandates secure storage and transmission of medical data
3. PCI DSS (Payment Card Industry Data Security Standard)
- Applies to businesses handling credit card transactions
- Ensures secure payment processing
- Requires strong encryption and access controls
4. ISO/IEC 27001 (International Organization for Standardization / International Electrotechnical Commission 27001)
- International standard for information security management
- Provides systematic approach to managing sensitive data.
- Focuses on risk assessment and continuous improvement
5. SOC 2 (Service Organization Control 2)
- Relevant for service providers handling customer data
- Evaluates security, availability, processing integrity, confidentiality, and privacy
Key Components of Cyber Security Compliance
Here are the essential components that form the foundation of effective cybersecurity compliance in an organization:
1. Risk Assessment
Organizations identify threats and vulnerabilities, assess likelihood and impact, and prioritize risks to protect systems and data and ensure business continuity.
2. Security Policies and Procedures
Defined policies and procedures guide employees in handling secure data, adhering to compliance requirements, and responding to potential security incidents.
3. Access Control
Access control mechanisms ensure that authorized users can access systems, applications, and sensitive information, preventing unauthorized breaches.
4. Data Encryption
Data encryption reduces exposure risk, ensures secure storage and transfer, and protects data confidentiality and integrity by transforming information into an unintelligible format.
5. Monitoring and Logging
Continuous monitoring and logging track activities, detecting anomalies, enabling timely threat identification and response, and maintaining security visibility.
6. Incident Response Plan
An incident response plan outlines procedures, roles, and responsibilities for detecting, containing, eradicating, and recovering from cybersecurity incidents, minimizing impact.
7. Regular Audits
Regular audits evaluate compliance standards, identify gaps, ensure control effectiveness, support continuous improvement, and strengthen security posture.
Cyber Security Compliance Process
Below is the key process organizations follow to establish and maintain effective cyber security compliance:
Step 1: Identify Applicable Regulations
Identify relevant laws and standards based on the industry location and data types to ensure a clear understanding of the full compliance requirements.
Step 2: Conduct Risk Assessment
Analyze system vulnerabilities, evaluate threats, and prioritize risks requiring immediate mitigation to protect organizational data assets effectively.
Step 3: Implement Security Controls
Deploy firewalls, antivirus software, encryption, multi-factor authentication, and other controls to safeguard systems against cyber threats.
Step 4: Develop Policies and Training
Create clear security policies, train employees on compliance requirements, and promote best cybersecurity practices across the organization.
Step 5: Perform Regular Audits
To confirm compliance, find loopholes, guarantee the efficacy of security controls, and consistently uphold regulatory adherence, conduct internal and external audits.
Step 6: Monitor and Update
Continuously monitor systems, update security measures, address emerging threats, and maintain a strong cybersecurity compliance posture consistently.
Benefits of Cyber Security Compliance
Here are the key benefits organizations gain by implementing effective cyber security compliance practices:
1. Improved Data Protection
Ensures sensitive information is securely protected from breaches, unauthorized access, and data leaks, maintaining confidentiality, integrity, and availability.
2. Reduced Financial Losses
Prevents costly data breaches, fines, penalties, and legal actions, reducing financial risks and protecting organizational assets effectively.
3. Competitive Advantage
Strong compliance practices build customer trust, enhance reputation, and provide organizations with a distinct competitive advantage in the market.
4. Better Risk Management
Identifies potential threats and vulnerabilities, enabling proactive risk mitigation strategies and ensuring consistent control over cybersecurity challenges.
5. Increased Operational Efficiency
Standardized processes streamline workflows, improve security management, reduce redundancies, and enhance overall operational efficiency across the organization.
Challenges in Cyber Security Compliance
Here are the common challenges organizations face while implementing and maintaining cyber security compliance:
1. Complex Regulations
Understanding multiple compliance frameworks across regions and industries becomes challenging, requiring expertise, time, and effort to implement correctly.
2. High Implementation Costs
Investing in security tools, employee training, audits, and infrastructure upgrades significantly increases overall costs, impacting organizational budgets.
3. Constantly Evolving Threats
Rapidly changing cyber threats require continuous updates, monitoring, and adaptation of compliance strategies to remain effective.
4. Lack of Skilled Professionals
A shortage of cybersecurity experts makes it difficult for organizations to implement, manage, and maintain compliance programs efficiently.
5. Integration Issues
Integrating compliance controls with existing legacy systems can be complex and time-consuming, and may disrupt business operations.
Real-World Examples
Here are some practical examples of how different industries implement cyber security compliance to protect data and ensure regulatory adherence:
1. Financial Institutions
Banks implement PCI DSS and other regulations to secure transactions, protect customer data, and prevent financial fraud risks.
2. Healthcare Organizations
Hospitals comply with HIPAA regulations to protect patient records, ensure confidentiality, maintain data integrity, and secure sensitive information.
3. E-Commerce Platforms
Online retailers follow GDPR and PCI DSS standards to safeguard customer data and payment details and ensure secure transactions globally.
4. Cloud Service Providers
Cloud providers adhere to SOC 2 and ISO 27001 standards, ensuring data security, availability, confidentiality, and reliable services.
Final Thoughts
Cyber security compliance is essential for modern businesses to protect sensitive data, reduce risks, and ensure regulatory adherence. By implementing strong security measures and staying up to date on evolving threats, organizations can build customer trust, improve resilience, and maintain a secure, compliant environment that supports long-term growth and operational success.
Frequently Asked Questions (FAQs)
Q1. Is cyber security compliance mandatory?
Answer: Yes, in many industries, compliance is legally required to protect sensitive data and ensure privacy.
Q2. How often should compliance audits be conducted?
Answer: Audits are typically conducted annually, but some organizations perform them more frequently based on risk levels.
Q3. Can small businesses achieve cyber security compliance?
Answer: Yes, small businesses can implement basic controls and follow relevant standards to achieve compliance.
Q4. What industries require strict compliance?
Answer: Industries such as healthcare, finance, e-commerce, and government require strict compliance.
Recommended Articles
We hope that this EDUCBA information on “Cyber Security Compliance” was beneficial to you. You can view EDUCBA’s recommended articles for more information.

