Automation has become indispensable for efficient system administration in today’s fast-paced IT landscape. Ansible, a powerful automation tool, simplifies complex tasks by automating configuration management, application deployment, and more. Ansible Inventory is at the heart of Ansible, a critical component that defines the systems you want to manage. By understanding and effectively utilizing Ansible Inventory, you can streamline your automation workflows and achieve greater efficiency and reliability in your IT operations.
What is the Ansible Inventory?
Ansible defines the infrastructure for automation tasks through its Inventory component. It is a collection of hosts, physical machines, virtual servers, or containers. The inventory file tells Ansible which systems to manage and how to connect to them, making it a central piece for ensuring that playbooks and commands run on the correct machines.
An inventory can range from a simple list of IP addresses or hostnames to a more complex structure with groups, variables, and dynamic scripts that integrate with cloud platforms. This flexibility allows Ansible to efficiently manage environments of any size, from a handful of servers to thousands spread across different data centers or cloud providers.
Why is Inventory Management Important?
Proper inventory management is critical for several reasons:
- Scalability: As environments grow, well-organized inventory files help maintain transparent and manageable structures, ensuring scalability.
- Efficiency: Grouping hosts and defining variables directly in the inventory improves the reusability of Ansible playbooks, reducing duplication and making automation more efficient.
- Consistency: Inventory management ensures that tasks are executed consistently across various hosts, reducing the risk of errors due to manual configuration.
- Flexibility: Dynamic inventory scripts and integrations allow for real-time data fetching from cloud platforms, adapting to infrastructure changes without manual intervention.
Types of Inventory Files
Static Inventory
Static inventory files are the simplest form of inventory management in Ansible. They are manually created and maintained, typically formatted using INI or YAML. The file specifies hosts and groups, allowing you to organize your infrastructure logically. This method is especially well-suited for relatively unchanged environments, such as small-scale deployments or traditional data centers.
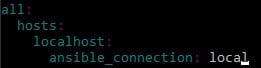
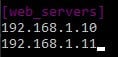
INI format
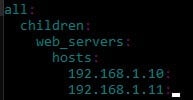
YAML format
Dynamic Inventory
On the other hand, dynamic inventory automates the host list generation process by using scripts or plugins that query external data sources. This type of inventory is essential for cloud environments, container orchestration platforms, or large-scale deployments where the infrastructure is constantly evolving.
How It Works: A dynamic inventory script or plugin queries cloud services (like AWS, Azure, or GCP) or other systems (e.g., Kubernetes, OpenStack) to generate an up-to-date list of hosts and their associated details. Ansible receives this real-time data and uses it to execute playbooks or ad-hoc commands.
Examples of Dynamic Inventory Sources
- AWS EC2: Ansible can pull information using plugins that connect to AWS, automatically listing instances and their metadata.
- Azure: The Azure inventory plugin fetches data on virtual machines within specified resource groups or subscriptions.
- Custom Scripts: Organizations can develop custom scripts to query internal databases or proprietary systems for host data.
Dynamic inventory significantly enhances Ansible’s capability to manage modern, fluid infrastructures by automating host discovery and reducing manual work. This capability makes it an indispensable tool for DevOps teams managing complex deployments.
Basic Inventory Concepts
Default Inventory Location
By default, Ansible looks for an inventory file at the path /etc/ansible/hosts. This file serves as the central reference point for host and group definitions. You can specify a custom inventory file when running Ansible commands by using the -i flag. This flexibility allows you to manage multiple inventory files for different projects or environments.
Command Example:
ansible-playbook -i custom_inventory_file.ini playbook.ymlInventory File Formats (INI vs YAML)
Ansible supports writing inventory files in INI or YAML formats. The choice between these two formats depends on user preference and the complexity of the environment.
- INI Format: The INI format is straightforward. It uses a section-header style to define groups of hosts, making it ideal for simple inventory structures.
- YAML Format: YAML offers more flexibility and readability, especially for complex hierarchies, nested groups, and variables.
Host Definitions
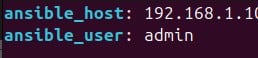
Hosts in an Ansible inventory file represent the machines or nodes that Ansible will manage. You can define hosts more readably using hostnames, IP addresses, or aliases.
Group Definitions
Groups help organize hosts with similar characteristics or roles. By defining groups, you can simultaneously apply playbooks or tasks to a collection of hosts, simplifying inventory management.
Example:
Host and Group Variables
Host Variables
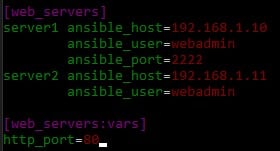
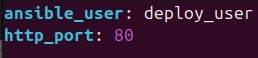
Host variables allow you to specify settings unique to a particular host in your inventory. These can be connection parameters (like ansible_user, ansible_host, ansible_port) or custom variables (like http_port, db_role, etc.) relevant only to that specific host.
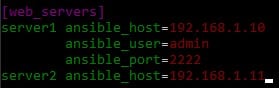
Example:
Explanation:
- In this case, server1 and server2 are hosts under the web_servers
- The host-specific variables (ansible_host, ansible_user, and ansible_port) specify how Ansible should connect to each server.
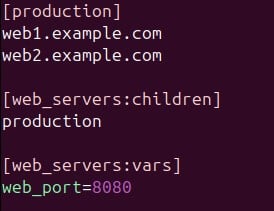
- Ansible applies the http_port=80 variable to all hosts in the web_servers group through the web_servers:vars, meaning every host in this group will use port 80 for HTTP services.
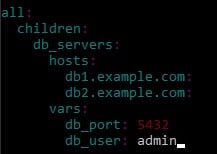
Group Variables
Group variables apply to all hosts in a specific group. You can define common settings for a set of hosts, reducing repetition in your inventory and making it easier to manage large hosts with similar configurations.
Example:
Explanation:
- Here, db_servers is a group containing example.com and db2.example.com as its hosts.
- The vars section within db_servers defines two variables: db_port (set to 5432) and db_user (set to admin).
- These variables will be applied to example.com and db2.example.com, making them suitable for managing multiple database servers with similar configurations.
Inventory Structure and Organization
Directory Layout Best Practices
When managing Ansible inventory for large-scale environments, structuring your inventory files in a well-organized directory layout is crucial. This practice helps maintain clarity, simplifies updates, and ensures that different environments or roles are easily accessible.
Best Practice Tips:
- Use a dedicated directory for each environment (e.g., production, staging).
- Group host files and variables by type (e.g., yml, group_vars/, host_vars/).
- Maintain a common directory for shared configurations applicable to all environments.
Example Directory Layout:
inventory/
├── production/
│ ├── hosts.yml
│ ├── group_vars/
│ │ ├── all.yml
│ │ ├── web_servers.yml
│ │ └── db_servers.yml
│ ├── host_vars/
│ │ ├── server1.example.com.yml
│ │ └── db1.example.com.yml
└── staging/
├── hosts.yml
├── group_vars/
│ ├── all.yml
│ ├── web_servers.yml
│ └── db_servers.yml
└── host_vars/
├── server2.example.com.yml
└── db2.example.com.yml
Explanation:
- yml: The main inventory file lists all hosts for a particular environment.
- group_vars/: A directory containing variable files that apply to specific groups.
- host_vars/: A directory containing variable files specific to individual hosts.
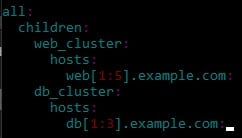
Group Organization Strategies
To manage large infrastructures effectively, organizing hosts into strategic groups is essential. Groups can represent different roles (e.g., web_servers, db_servers), environments (e.g., production, staging), or regions (e.g., us-east, eu-west).
Example:
Parent-Child Group Relationships
Ansible supports hierarchical grouping, where groups can be nested within other groups. This grouping enables you to build an inventory with layered configurations and shared settings.
Example:
- Parent Group: all
- Child Groups: production, staging
- Nested Groups: web_servers, db_servers
With parent-child relationships, you can apply overarching variables or configurations to a parent group, which its child groups then inherit.
Host Patterns and Ranges
Host patterns and ranges are mechanisms in Ansible’s inventory file that help concisely define and manage large numbers of similar hosts. Instead of listing each host individually, you can use range patterns and host groups for simplicity and scalability.
- Range Patterns: Using the [start:end] range syntax, you can specify sequentially named hosts.
- Combining Patterns: You can also combine host patterns to target specific hosts or groups.
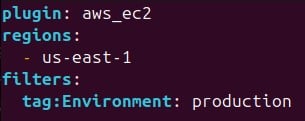
Dynamic Inventory
Dynamic inventory refers to using scripts or plugins that automatically generate an inventory of hosts by querying external data sources. This inventory is useful when managing dynamic infrastructure where servers, such as cloud-based environments or containerized platforms, frequently change. Unlike static inventory, which is manually updated, dynamic inventory provides real-time updates of available hosts.
Inventory Plugins vs Scripts
Inventory Plugins
Pre-built modules provided by Ansible for integration with popular services (e.g., AWS, Azure, GCP).
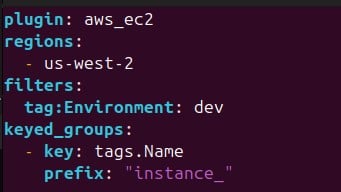
Example: The aws_ec2 plugin lets Ansible fetch host details directly from AWS.
Usage: Plugins are simple to configure and require only a configuration file in YAML format.
Custom Scripts
User-defined scripts that query custom sources such as databases or internal APIs.
Output Requirement: The script must output JSON-formatted data that Ansible can interpret.
Example: A Python script querying a company’s internal API for server details.
{
"web_servers": {
"hosts": ["web1.example.com", "web2.example.com"],
"vars": {
"http_port": 8080
}
}
}Cloud Provider Integration
Using plugins, users can integrate dynamic inventory with cloud platforms like AWS, Azure, and Google Cloud.
AWS Example
Configure the aws_ec2 plugin in a file.
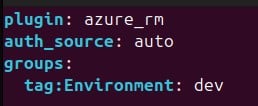
Azure Example
Use the azure_rm plugin to gather inventory data from Azure VMs.
Inventory Variables
Inventory variables in Ansible allow you to customize and manage configuration settings specific to hosts or groups of hosts. These variables can define connection details, roles, or custom data relevant to your deployment.
Defining Variables in YAML format
Users can define variables in separate YAML files within an inventory directory structure:
group_vars/web_servers.yml
host_vars/web1.example.com.yml
Variable precedence:
Ansible variables follow a specific order of precedence, determining which variable values override others. The order, from lowest to highest precedence, is as follows:
- Role defaults.
- Inventory file or script group vars.
- Inventory group_vars/all.
- Inventory group_vars/*.
- Inventory file or script host vars.
- Inventory host_vars/*.
- Playbook group_vars.
- Playbook host_vars.
- Host facts gathered with gather_facts.
- Registered vars.
- Set_facts.
- Variables defined in tasks or playbooks.
- Extra vars (e.g., via the command line with -e) always have the highest precedence.
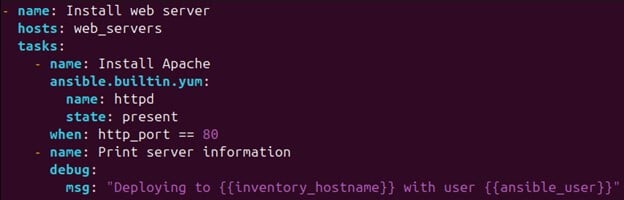
Using Variables in Playbooks:
The {{ variable_name }} syntax can reference variables in playbooks.
Example:
Variable Inheritance:
Variables can inherit from parent groups. For example, if web_servers is a child production group, it will inherit any variables defined for the production group unless overridden.
Example:
Conclusion
In conclusion, mastering Ansible inventory management is essential for efficiently handling infrastructure, especially in complex environments. Understanding the basic and dynamic inventory structures empowers users to define hosts and groups flexibly while leveraging plugins or custom scripts for dynamic setups. Host and group variables offer potent ways to configure environment-specific settings, and knowledge of variable precedence ensures precise control over their application. Incorporating best practices, such as organizing inventory files and securing sensitive variables, enhances operational clarity and security. By fully utilizing Ansible’s inventory capabilities, IT professionals can automate, scale, and manage deployments effectively, reducing manual efforts and minimizing errors, ultimately leading to more streamlined and reliable infrastructure management.
Recommended Articles
Here, we discuss the Introduction and how to use an Ansible inventory. Along with different examples and code implementation. You may also have a look at the following articles to learn more –