Updated March 16, 2023
What is Advanced Encryption Standard (AES)?
The advanced encryption algorithm(AES) is an asymmetric algorithm. Advanced Encryption Standard(AES) came into play since the key size of DES is very small.
Key features of AES:
- Symmetric key symmetric block cipher.
- Data of 128 bits.
- Compared to triple-DES, it tends to be faster and stronger.
- Design details and specifications are complete.
- Java and C languages can be used for implementation.
Advanced Encryption Standard (AES) Encryption
It works on a substitution permutation network where a series of different operations are linked together. Here all the computations are carried out as bits instead of bytes. The Advanced Encryption Standard(AES) case treats every 128 bits of blocks into a 16-byte segment. Every 16-byte segment gets settled as a 4 and 4 bytes matrix. The length of the key determines the number of rounds involved.
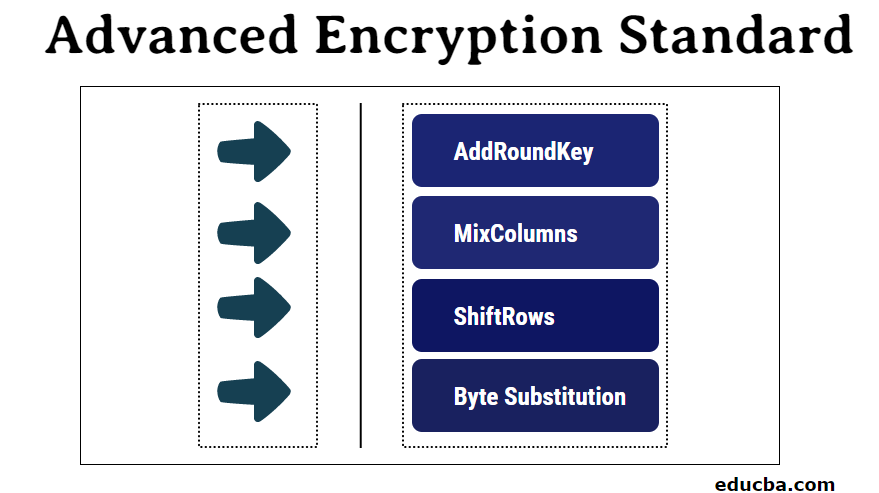
Every round holds four subprocesses, the steps involved in each of the processes are listed below:
1. Byte Substitution (SubBytes)
By referring to a fixed table, the 16 input bytes are substituted in a specific design. Again a four-row, four-column matrix is formulated.
2. ShiftRows
A left shift is applied to each of the four rows; All exceeding entries are entered on the right side.
The process involves:
- No shift to the first row.
- Shift the second row by one left position.
- Two-position shifted to the left for the third row.
- From the fourth row, make a three-position shift.
- A brand new matrix is formed with the same 16 bytes but associated with several positional changes.
3. MixColumns
A profound mathematical function is now applied to each of the four-byte columns. Here the process absorbs 4 bytes from one column and completely transmutes the four bytes into 4 different bytes. Hence another new matrix is created, and again it’s of the same 16 bytes and 4 * 4 format.
4. AddRoundKey
The 16 bytes are now measured as 128 bits and then XORed to a round key of 128 bits. The output forms the needed ciphertext if this is the last round of the encryption segment. If else the resultant 128 bits are construed as 16 bytes and commence one more alike round.
Decryption Process
The decryption process is very similar to the encryption process, but this works in the reverse of the same process, hence as like encryption here, each round consists of the four processes carried out in the reverse order.
- Add round key
- Mix columns
- Shift rows
- Byte substitution
For Advanced Encryption Standard (AES) cipher, encryption and decryption must be separately applied and implemented.
Advantages of Advanced Encryption Standard (AES)
The following advantages are mentioned below:
- It implies be a very robust protocol since this can be applied to both hardware and software.
- It is also very robust for hackers because of its large key sizes. The key sizes used here are very higher as like 128, 192, and 256 bits for encryption.
- A large set of applications such as e-business, data storage in an encrypted format, and wireless communication make use of these Advanced Encryption Standard(AES) protocols to a large extent.
- Commercially his cipher protocol is among the most widely used ones all around the world.
- Hacking becomes a nightmare process here.
- Ever 128 bits expect more than 2128 attempts to decipher; this makes the cipher highly secure and almost impossible to hack.
Why is Advanced Encryption Standard (AES) Used?
Being the Advanced Encryption Standard(AES), a key standard for cryptography is in the process of data encryption and privacy. It acts as the most popular cipher and used for a wide range of applications comprising even the US Government use AES for ensuring data privacy and security. Advanced Encryption Standard(AES) is symmetrical and stands away from the stream cipher where each character is encrypted one at the moment. Sysmetricity means the same kind of keys is used in the encryption process. It is also very robust for hackers because of its large key sizes. The key sizes used here are very higher as like 128, 192 and 256 bits for encryption. Commercially his cipher protocol is among the most widely used ones all around the world.
The highlighted features of these block ciphers are as below:
- Symmetric key symmetric block cipher.
- Data of 128 bits.
- Compared to triple-DES, it tends to be faster and stronger.
- Design details and specifications are complete.
- Java and C languages can be used for implementation.
Audience for Advanced Encryption Standard (AES)
The audience for advanced encryption standards is:
- Audience interested to learn about Advanced Encryption Standard(AES).
- Professionals are willing to elevate their skills in cryptography and data security.
- professionals who are willing to penetrate and caliber themselves in data and information security oriented divisions.
- It helps to move forward the professional aspects and technological skillset of professionals who are intended to do the same.
Conclusion
Advanced Encryption Standard positions itself is among the most robust and scalable cryptography algorithms or protocols in the world of security and is expected to continue its classified expansion wide across various security networks in the stream of information technology.
Recommended Articles
This is a guide to Advanced Encryption Standard. Here we discuss AES encryption process, its uses, along with advantages and audience interested in learning. You may also look at the following articles to learn more –


