Overview of IPv4 Header Format
IPV4 header format is of 20 to 60 bytes in length, contains information essential to routing and delivery, consist of 13 fields, VER, HLEN, service type, total length, identification, flags, fragmentation offset, time to live, protocol, header checksum, source IP address, Destination IP address and option + padding, where each has its own features and provides essential data required to transmit the data.
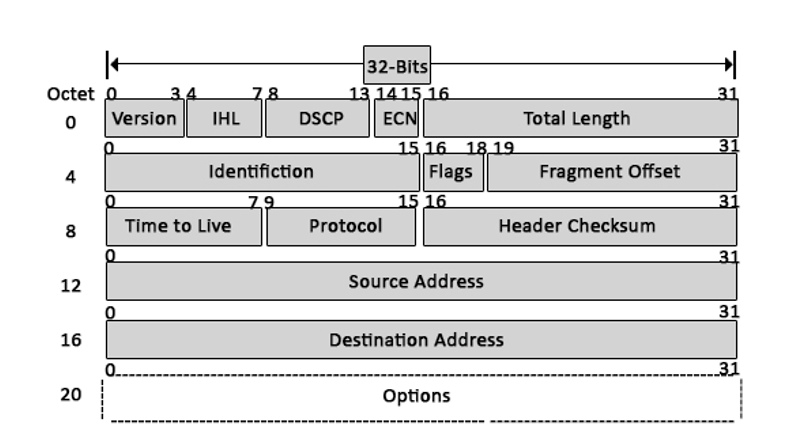
An IPv4 packet header has a total of 14 fields; among these 14 fields, only one is optional, which is aptly known as the options component.
IPv4 Header Format Component
Below is the list mentioned.
- Version
- Internet Header Length
- Type of Service
- Explicit Congestion Notification
- Total Length
- Identification
- Flags
- Fragment Offset
- Time to live
- Protocol
- A checksum of header
- Source Address
- Destination Address
- Options
Let’s take a look at these components, their sizes and what they can do:
- Version: The first header field is a 4-bit version indicator. In the case of IPv4, the value of its four bits is set to 0100, which indicates 4 in binary.
- Internet Header Length: IHL is the 2nd field of an IPv4 header, and it is of 4 bits in size. This header component is used to show how many 32-bit words are present in the header. As we know, IPv4 headers have a variable size, so this is used to specify the size of the header to avoid any errors. This size can be between 20 bytes to 60 bytes.
- Type of Service: ToS is also called Differentiated Services Code Point or DSCP. This field is used to provide features related to service quality, such as for data streaming or Voice over IP (VoIP) calls. It is used to specific how a datagram will be handled.
- Explicit Congestion Notification: ECN is used to send notifications to the sender or receive in situations where network congestion happens. This is an optional feature of IPv4 can; if one of the endpoints don’t support it, it is not used.
- Total Length: This field’s size is 16 bit, and it is used to denote the size of the entire datagram. The minimum size of an IP datagram is 20 bytes, and at the maximum, it can be 65,535 bytes. Practically, all hosts are required to be able to read 576-byte datagrams. If a datagram is too large for the hosts in the network, fragmentation is used, which is handled in the host or packet switch.
- Identification: The identification or ID field in a packet can identify an IP datagram’s fragments uniquely. Some have suggested using this field for other things such as adding information for packet tracing etc.
- Flags: flag in an IPv4 header is a three-bit field that is used to control and identify fragments. The following can be their possible configuration:
- Bit 0: this is reserved and has to be set to zero
- Bit 1: DF or do not fragment
- Bit 2: MF or more fragments.
- Fragment Offset: This field is 13 bit long in length, and it is measured by blocks that units of 8-byte blocks. These are used to specify the offset of a fragment relative to the start of the IP datagram, which when it was not fragmented. As you can expect, the first offset of a fragment is always set to zero. The maximum possible offset is ( 213-1 ) * 8 = 65528, but it is more than the maximum possible IP Packet length, which is 65,535 bytes long with the length of a header added in.
- Time to live: Time to live (or TTL in short) is an 8-bit field to indicate the maximum time the datagram will be live in the internet system. The time here is measured in seconds, and in case the value of TTL is zero, the datagram is erased. Every time a datagram is processed, it’s Time to live is decreased by one second. These are used so that datagrams that are not delivered are discarded automatically. TTL can be between 0 – 255.
- Protocol: This is a filed in the IPv4 header reserved to denote which protocol is used in the later (data) portion of the datagram. For Example, number 6 is used to denote TCP and 17 is used to denote UDP protocol.
- The header’s checksum: The checksum field is of 16-bit length, and it is used to check the header for any errors. The header is compared to the value of its checksum at each hop, and in case the header checksum is not matching, the packet is discarded. Keep in mind that this is only for the header, and its protocol handles the data field. UDP and TCP, for example, have their own checksum fields.
- Source Address: It is a 32-bit address of the source of the IPv4 packet.
- Destination Address: the destination address is also 32 bit in size, and it contains the receiver’s address.
- Options: This is an optional field of the IPv4 header. It is used only when the value of IHL is set to more than 5. These options contain values and settings for things related to security. Record route and time stamp etc. You will find that the list of options component ends with an End of Options or EOL in many cases.
Conclusion
IP headers are one of the crucial components of the protocol. Being able to tell the network about the datagram, its source, and its destination is important, and so is the ability to detect any errors in the header to avoid using corrupted packets. Considering that almost all of the modern internet relies on IPv4 and IPv6, these headers are used in almost all of the HTTP internet traffic.
Recommended Articles
This has been a guide to IPv4 Header Format. Here we discussed Introduction to IPv4 Header Format, its components with their sizes and what they are used for. You can also go through our other suggested articles to learn more –


