Updated November 30, 2023
Introduction to Deadlocks in Operating System
A situation when the processes are blocked due to the unavailability of resources is called deadlock. The resources are being held by other processes and they wait for resources from a different process. This happens in Operating System as well and this is called deadlocks in the operating system. In OS, two or more process holds the resources and wait for another process to release their resources. The three ways to avoid deadlock is to avoid or prevent the problem altogether, detect and recover the resources, and ignore the problem. Windows and UNIX are known for ignoring the problem and the system reboots when this happens.
What is Deadlock?
- The process tends to happen in an OS with the help of resources. First, the process requests some resource to the OS. If the resource is available readily, OS grants the resource. If not, OS makes the process wait. Once the resource is available for the process, it is used and the process is completed. When the process waits for the resource that is assigned to another process, deadlock happens.
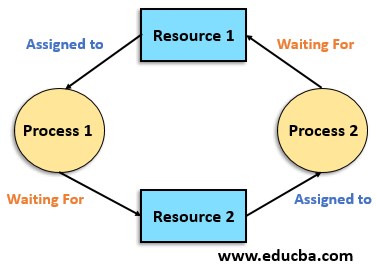
- Deadlock occurs when four conditions occur together. When one resource can be used only by one process at a time, deadlock happens. Also, it happens when the process is holding the resource and waiting for other resources. The resource belongs to the process in such a way that other processes cannot claim this resource unless this is released from the process. When the processes are waiting for each other one after the other, deadlock happens. We can conclude the conditions as mutual exclusion, hold and wait, no preemption, and circular wait.
- Let us consider three processes P1, P2, and P3 that use R1, R2 and R3 sequentially. While doing the process, P1 requires R2. Since P2 is using R2, the P1 process is stopped and waiting for P2 to get completed. Now, P2 needs R3 and hence, P2 is also stopped. Simultaneously, P3 needs R1 and since it is used by P1, P3 also comes to a halt. This explains the process of deadlock. This is the process of circular wait in deadlock.
- The system becomes irresponsive as all the processes are at a halt. Now no progress is made in the process and the system waits for the process to respond which we usually see in our system.
- There is another form of deadlock called livelock. A condition when two or more processes continuously change their state when the changes happen in other processes thus resulting in no work is called livelock. This is called deadlock in a way that no progress is made to the process through the resources are not held or the process is not waiting for any resources.
- Another situation called starvation happens when a low priority process gets blocked and a high priority process progresses its way. The situation is not infinite but it’s long waiting. When comparing starvation with deadlock, every deadlock is starvation but every starvation is not a deadlock. When the resource is requested in starvation, the resource is used by high-priority processes. It happens due to mismanagement and priority task assignments in an uncontrollable manner.
- In multiprocessing, deadlock happens frequently as different processes need particular software to function.
- The deadlock has some advantages as well. When a single activity has to be carried out, deadlock helps. The resource is released voluntarily when the process is completed. When the state of resources is stored and saved, deadlock turns out to be an easy method. When a deadlock is needed, it can be enforced by compilation time checking. We cannot solve the problem by computation and it is solved only by system design.
Methods to Handle Deadlock in Operating System
In order to handle deadlock, there are four methods:
1. Ignoring the Deadlock
this approach is taken into consideration by windows and UNIX mostly for end-user processes. When the system is used only for browsing and other normal processes, this method is suitable. The system just ignores the deadlock and pretends that it had never occurred. Performance of the system decreases if the deadlock is handled always. When a single process has to be carried out always and if deadlock happens, restarting the system is the best solution recommended. And deadlock in the end-user system does not happen always. So it is better to avoid handling it.
2. Preventing the Deadlock
If among the four conditions of mutual exclusion, hold and wait, no preemption, and circular wait, one condition is violated, and then deadlock will not happen in the system. This method helps to prevent deadlock. There can be other issues while violating one condition and care should be taken for the same.
3. Avoiding Deadlock
operating system checks for each step of the process to know whether it is in a safe state or in an unsafe state. If the system reaches an unsafe state, the system retraces the step and does the process again. In this manner, deadlock is avoided. The process is time-consuming and not always recommended.
4. Detecting Deadlock and Recovering the Process
resource allocation graph is used to detect the deadlock. The detection is either single instanced or multiple instanced. Detection of the cycle helps to determine whether deadlock happened or not in a single instance. The resource allocation graph is converted into an allocation and request matrix to apply a safety algorithm to the system. Resources or processes are considered for recovery. A resource is chosen and released from one process and given to the other process expecting it to be completed sooner. Or the system rolls back to the previous safe state when it reaches the deadlock state. There should be a checkpoint in each state for the rollback. The process is entirely delayed due to deadlock. The resource needs are often not taken into consideration when the process is delayed by the system. It is better to avoid the deadlock or sort it out rather than delay the process.
Recommended Articles
This is a guide to Deadlock in Operating System. Here we discuss what is Deadlock and its methods to handle Deadlock in Operating System. You can also go through our other suggested articles to learn more –