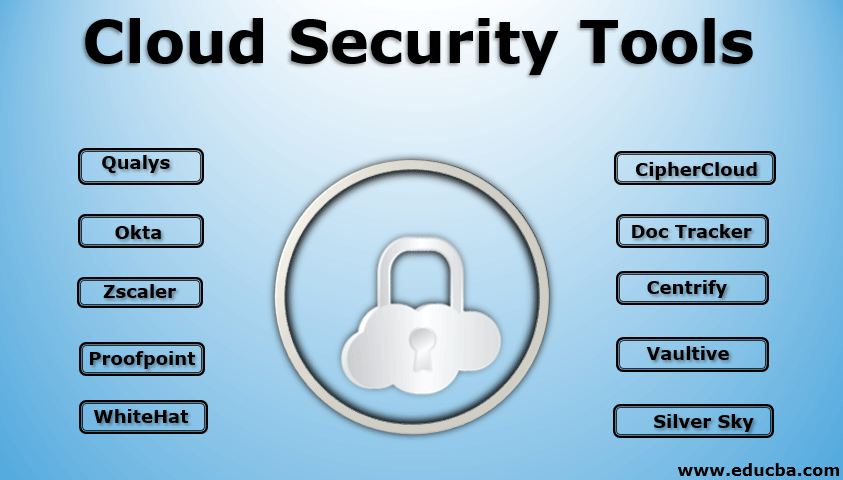
Introduction to Cloud Security Tools
Cloud Security tools(like Qualys, WhiteHat Security, Okta, Proofpoint, ZScaler, CipherCloud, DocTracker, Silver Sky, etc.) help provide cloud security, which falls into two broad categories based upon the issue faced by the users, i.e., issues faced by cloud providers and the issues faced by the customers, these tools are promising and easy to install in the software and hardware systems and helpful in preventing any data loss, data leakage or any data snaps from the hackers.
Top Cloud Security Tools
The company’s size is not a matter when it comes to security. Even the mobile phone has many passwords and pattern locks to protect the user data. Hackers are spread every place to snap the data whenever there is a poor firewall. So, security is the first one mandatory to be checked periodically. Here are a few security tools that are promising and pocket-friendly to be installed on your hardware and software systems.
1. PingSafe
PingSafe is an agentless CNAPP platform designed for various industries and companies of all sizes. It is equipped with CSPM, CWPP, and CDR solutions, detecting online vulnerabilities and addressing new threats. It automates compliance checks, monitors IaC security, and identifies cloud misconfigurations across multiple environments. PingSafe works on different platforms like GitHub and GitLab, scanning for over 800 types of secrets in real time. Plus, it has a user-friendly interface and is simple and resource-efficient.
2. Qualys
You install the Qualys tools to check for any threats and secure your devices, web applications, and web pages through cloud solutions. The organization analyses any malware attack and ensures that the User’s data or system is unaffected. If it finds any attack, it displays the required steps to solve the issues and again scans all the web pages and applications to get it clear and work efficiently. Qualys produces a cloud-only firewall to protect web pages from any threat.
3. Wiz
Wiz is a cloud security company that focuses on providing cloud visibility and security solutions. Wiz is known for its cloud security platform that helps organizations discover, assess, and mitigate security risks in their cloud environments, such as its Continuous Security Posture Management (CSPM) and Cloud Workload Protection Platform (CWPP) solutions. These are designed to enhance cloud security posture by identifying vulnerabilities, misconfigurations, and potential threats across cloud infrastructure.
4. WhiteHat Security
WhiteHat Security aims to protect the user websites from the root level, which includes the coding process. This tool is available as a suite pack embedded with five different applications. The first application is used to protect web pages and coding. The second application helps to identify the issues detected before the website launched during its pre-production time. Another app helps users check any major issues in the live environment. The fourth application allows the user to access the web pages even through holes when any patch is detected. The major one acts as a research arm and provides you alarm with updated information on the user security network.
5. Accuknox
AccuKnox is the industry’s most comprehensive Zero Trust CNAPP (Cloud Native Application Protection Platform) Tool that secures Build to Runtime. It combines agentless CSPM (Cloud Security Posture Management) and eBFP, LSM-powered CWPP (Cloud Workload Protection Platform). AccuKnox is an innovative cloud security tool with 10+ Patents and supports IoT/Edge and 5G workloads.
6. Okta
Okta focuses on identity management about any person logging in and what is the reason behind their login. It already has the databases of the employees who log in daily for basic health checks and performance checks; then it has the details of clients, cloud service providers, and third-party customers. It knows about the people working at backends and forward-facing access to people. It helps users manage applications, including Salesforce, workday, and Microsoft office suite 365. It can also track data privacy agreements, sign-on buttons, and login dashboards.
7. Proofpoint
Hackers find Email, which Proofpoint, a tool focusing solely on Email, automatically generates from the weak hole across the systems. It prevents incoming data and ensures every single unit of outgoing data. It helps in the prevention of data loss. It also works on encryption and decryption of data handling and data flow.
8. Zscaler
Compared to ancient security methods, organizations apply the CipherCloud product from the Direct cloud network for cost-efficient and easy deployment. The company product Zscaler protects the systems from advanced threat attacks by monitoring and controlling the traffic that enters and flows out of the user network, which acts as a check post. It also secures and monitors the mobile phone with a special online mobile application dashboard.
9. CipherCloud
CipherCloud secures all the other services and products, including Google applications, Amazon web services, Chatter, and Office 365. It assures data protection through encryption, regularized traffic monitoring, and anti-virus scan.
10. Doc Tracker
Doc Tracker is at the top of the security layer, which shares the files from Box and Office 365. The user should apply a security layer on top of the files; anyone can read, edit, and control it if they forget. Doc Tracker focuses on preventing the documents from this kind of scenario. It enables the user to know about the other person who will access the shared file. If he tries to handle it from his limits, the user can retake the file by clicking “ unsharing.”
11. Centrify
Centrify aims at identity management across several applications and devices. The company policies aim to create a central area where users, employers, and customers can resemble each other and be viewed and accessed. It gives an alarm when a person tries to sign in from on-premise cloud software or cloud applications. It is a unique product that works for Samsung Knox, with added protection software features. This product allows the only sign-on process.
12. Vaultive
Vaultive acts as a transparent network proxy between cyberspace and the network without preface equipment. Before using the cloud-based servers, do not expect the company to provide complete security for users’ files and data; instead, practice protecting your data by encryption before it enters the servers. Vaultive encrypts every outgoing data from Office 365 before entering the networks and applications.
13. Silver Sky
It needs to be a user one-stop shop for cloud-based security. It provides email monitoring and network protection. It promotes the user to become a client of HIPAA and PCI agreements. This major client regulates an enterprise’s company policies, healthcare information, and online payments by giving strong multi-layer security systems.
Conclusion
That is why security as a service must be deployed and used effectively across the network to prevent data leakage, loss, and snap from hackers.
Recommended Articles
This is a guide to Cloud Security Tools. Here we discuss the introduction and different cloud security tools which are promising and pocket-friendly to install on your hardware and software system. You can also go through our other related articles to learn more-