Updated July 28, 2023
Introduction to VLAN
VLAN is Virtual Local Area Network that can connect multiple devices and machines in a single network, without having to place the devices in same geographical location. This type of network is chosen for its most favored features, which includes, cost efficiency as you get what you pay for, high-performance efficiency, flexible and much more scalable as the size of the network is not expected to be proportional to the physical area of the devices’ location, lower security risks given the network pattern, etc
The computer networks can be formed either with LAN (Local area network) or with WAN (Wide area network) through workstations, switches, bridges, hubs, devices, and servers. If they are at one location then they are referred to as LAN which is also called a broadcast domain. Several networks are connected virtually or logically as one LAN. In this, the packet is not sending to all the devices which are in-network but to a specific broadcast domain.
Every Virtual LAN has a unique broadcast domain. For different Virtual LANs, Layer 3 devices require to communicate while the same Virtual LAN switch is used. In Virtual LANs, Layer 3 devices separate the broadcast domain and Layer 2 header failed to verify one network from another.
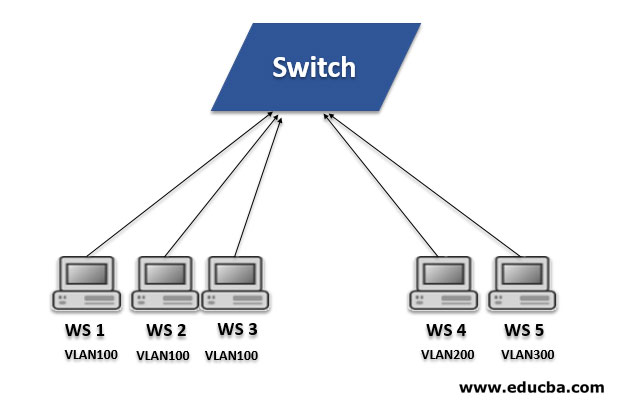
Fig. Example
- In the above example, 5 workstations are connected to the Layer 2 switch which supports it. Workstation 1, workstation 2 and workstation 3 are connected 100 while Workstation 4 & 5 are connected VLAN 200. Here WS1, WS2 & WS3 are connected to the same Virtual LAN, hence they included in the same broadcast domain. Here, the switch is able to send a packet between workstations WS1, WS2 & WS3.
- Similarly for WS4 & WS5 switch will send the packets. As they are in the same VLAN there is no need for Layer 3 device. However, without Layer 3 devices like router, WS1 & WS4 will not be able to communicate with each other. Similarly, WS2 or WS3 will not be able to communicate with WS5 without the Layer 3 device. Therefore, Layer 3 devices needed to communicate between workstations that are on different LAN.
- It can be configured by setting parameters like VLAN number, name, state, type, MTU (maximum transmission unit), SAID (Security Association Identifier). Before the configuration, VTP (VLAN Trunking Protocol) is used to store information on the global VLAN configuration of the network. The vlan.dat file contains VLAN configuration data which is stored in flash or NVRAM.
- In th, individual or groups of ports are connected. Any host or workstation connected to these ports or ports included Virtual LAN. It is called statically configuration of the host into the network. With respect to the MAC address, the host can be connected dynamically to Virtual LAN. A separate database is maintained the MAC address to VLAN connections. For this VMPS functionality is developed by CISCO. VMPS stands for Membership Policy Server.
Ranges of Virtual LAN
The range is categorized into Reserved, Normal & extended respectively.
Following are the ranges:
| VLANs | Range | Usage |
| VLAN 0, 4095 | Reserved | These are reserved for system use only. It can’t be seen or used. |
| VLAN 1 | Normal | It is a Cisco default Virtual LAN which has all switch ports and which can’t be edited or deleted but can be used. |
| VLAN 2-1001 | Normal | These Virtual LANs can be created, edited and deleted. These are used for Ethernet VLANs. |
| VLAN 1002-1005 | Normal | These Virtual LANs are Cisco defaults for token rings & FDDI and can’t be deleted. |
| VLAN 1006-4094 | Extended | These Virtual LANs are configured for extended range and only used for Ethernet VLANs. |
Important Features
Following are the features :
- Security: Network administrators can add additional security to network communication by implementing Virtual LAN. Data will be more secure by creating Virtual LAN as it can set up firewalls, it can control broadcast domains and it can also restrict access.
- Performance: It increases performance, as it reduces the traffic load by avoiding unwanted destinations. Only for requested devices will get multicast packets, not all the devices which are connected in the network when traffic is of broadcast & multicast.
- Grouping: Virtual LANs can group or configure logically with respect to their domain areas irrespective of geographical locations of the devices.
- Scalability& Flexibility: As discussed above, Virtual LANs can be added, deleted the number of a host as per requirement. Using VLANs relocation of the network is simple. It also allows for the expansion of the network. Hence, we can say that Virtual LANs are flexible.
- Cost-effective: These are cost-effective, as they are used to create broadcast domains, hence reduces the requirement of costly routers.
Conclusion
A Virtual LAN is group workstations, network servers, and other network devices, irrespective of geographical locations they act as a single broadcast domain. We have discussed ranges such as VLAN 0 & 4095, VLAN 1, VLAN 2-1005 and VLAN 1006-4094. Security, performance, the formation of virtual groups, flexibility, scalability and cost-effective are the key features. Using Virtual LAN, a small size network can be created which is simple to handle. To communicate within the same VLAN switch is required while for different VLANs Layer-3 devices (e.g. Router) are needed.
Recommended Articles
This is a guide to What is VLAN? Here we discuss what is VLAN? along with the features, and ranges of Virtual LAN along with the respective Diagram. You can also go through our other related articles to learn more–