Updated June 9, 2023
Introduction to Storage Network Area
The following article provides an outline for What is Storage Area Network? Information or data which is a company asset is the underlying resource on which all the computing processes are dependent. There are different enterprises and client’s products which are used to store these data.
Data can be stored in a different type of storage devices:
- Magnetic Storage Devices: Hard disk drive and Magnetic tape.
- Optical Storage Devices: Blu-ray, disc, DVD, and CD.
- Flash-based Storage Devices: Solid-state drive, memory card, and USB thumb drive.
How does Storage Area Network Work?
Storage devices are assembled within a storage system that provides high capacity, scalability, performance, and security.
This information is accessed by applications that are running on a server from different storage devices. The information is a unique company asset. Information is created and stored and accessed every second of every day which is the reason for currency inflow and outflow in all Enterprise businesses. In order to ensure that any business delivers the expected results, they must have access to accurate information and without any low latency. The management and protection of this business information are very important in order to deliver the expected results and for best business practice. Here we will see the concept of a network, storage, and storage area network (SAN), which is regarded as the ultimate response to all of these needs.
Storage Area Network is a collection of clients (Laptops, Desktops) which are used for local storage in the hard disk and other devices like enterprises and central repository – that are interconnected by communication channels. Because of these channels or network users/ enterprise service providers can achieve the efficient sharing of resources, services, and information among the network.
In simpler words or in Layman’s terms so that the common people can understand the topic or concepts of the network.
It is impossible to imagine today’s world as stand-alone human beings, with nobody that nobody communicates with. Much more importantly, it is impossible to imagine how human beings can work without using their body organs or senses. In our human world, we are sure you will agree with us that communication between any two individuals makes a significant difference in all aspects of life. Communication in any form is not easy, and we need many components in order to communicate with others.
Factors consist of a common language – which needs to be communicated, a medium where the communication will flow, and finally, there should be an endpoint from which we need to be sure that communication was received and understood. So in today’s world, we use language as a communication set of rules, and sounds and writing are the communication media. Just like this, a computer network needs almost the same components as our example as mentioned above, but a difference is that all these factors need to be controlled to ensure effective communications.
What is the Storage Area Network?
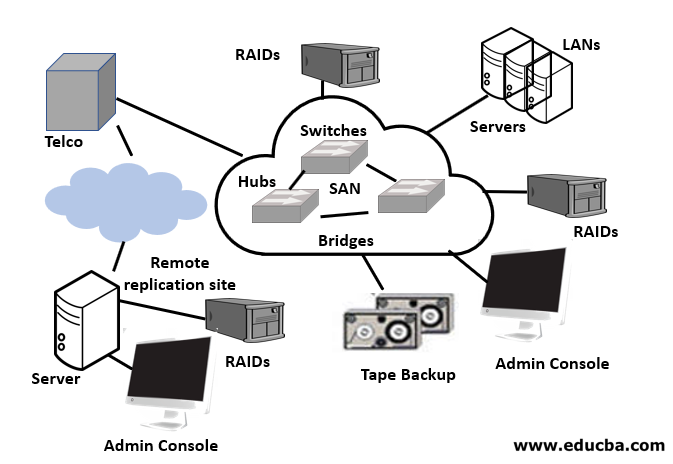
A SAN is a special high-speed network that stores and provides access to large amounts of data.
RAID: It is a technique that combines multiple disk drives into a logical unit which is called a RAID set and provides protection and performance.
- Provides data protection against drive failures.
- Improves storage system performance by serving I/Os from multiple drives simultaneously.
- Two implementation methods.
- Software RAID implementation.
- Hardware RAID implementation.
LAN: A LAN (Local Area Network), is a network that establishes a network in a small geographical area such as homes or offices.
WAN: A WAN, (Wide Area Network), is a network that establishes a network over larger geographical areas.
Different Types of Storage Area Network
Given below are the different types of storage area network:
1. Fibre Channel Protocol (FCP)
Fibre Channel Protocol is used to transfer the data with very high speed between the initiators and the target i.e. between the client and the storage system. In these, all the cluster of storage devices is connected to the switch with the cables. It has a bandwidth between 2- 16 Gigabytes per second.
2. Internet Small Computer System Interface (iSCSI)
SCSI is a system that can interact with storage media. Like if you get a hard drive – it is connected by SCSI. iSCSI is the ability to access the network drive remotely by using TCP protocol.
3. Fibre Channel over Ethernet (FCoE)
Fibre Channel over Ethernet (FCoE) is used as a medium for the traffic of LAN and SAN which will result in the less no. of server adapters. Like in LAN we use NIC (Network Interface Card ) as an adapter and in SAN there is HBA ( Host box adapters) but in FCoE – we will be using only one adapter i.e. CNA ( converged network adapter) which has the understanding to differentiate between the SAN and LAN traffic.
4. Non-Volatile Memory Express over Fibre Channel (FC-NVMe)
NVme used for higher scalability, efficiency and low latency. It can transfer the data with 20 microseconds or less.
Advantages of Storage Area Network
Or
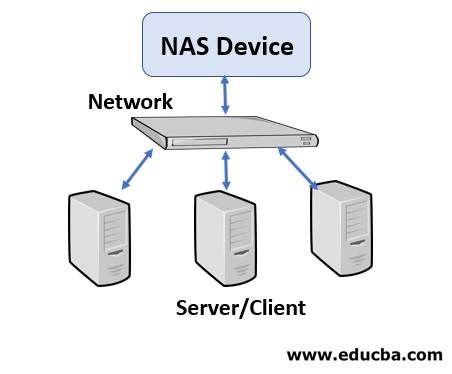
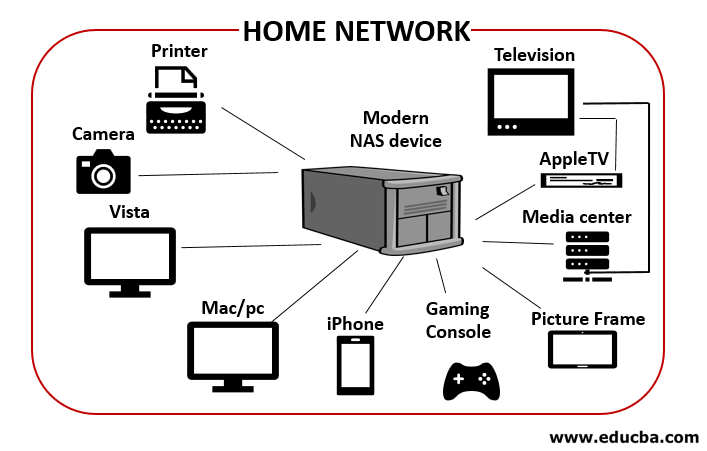
In NAS, there is a central repository from where we can access the data to different client and Enterprise products using LAN i.e users on Local Area Network can access the data through the central repository. So there is only one line for data transmission which can fail anytime and any organization can lose the business.
But in the case of SAN, there is a network between all the storage devices so that we can access them through multiple lines. In short, data accessing failure chances are very less. So large enterprise service providers use SAN.
Conclusion
In order to maintain or ensure that any business delivers the expected results, they must have access to accurate information and without any low latency. It is also important for the management and protection of this business information in order to deliver the expected results and for the business to grow.
Recommended Articles
This is a guide to What is Storage Area Network? Here we discuss what is storage area network? along with the types and advantages of the storage network. You can also go through our other related articles to learn more –


