Updated May 24, 2023
Introduction to Risks of Cloud Computing
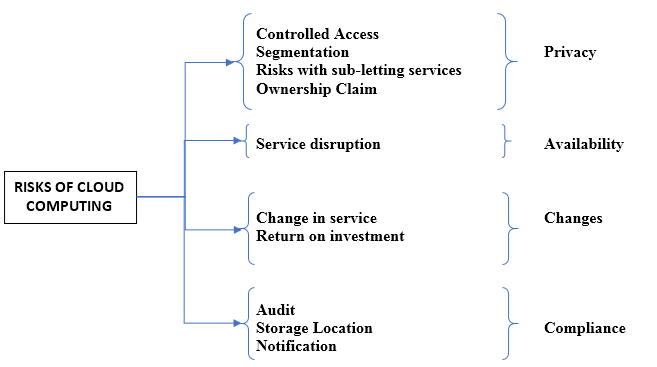
Being an on-demand availability of system resources, like computing power and data storage, cloud computing involves various types of risks that are grouped into different categories like privacy (involves risks like controlled Access, Segmentation, Risk with Sub letting services, and ownership claims), availability (involves risk like service disruption), changes (involves risk like Changes in service and return of investment) and compliance( involves risk like Audit, storage location, and notification).
What is Cloud Computing?
Now to understand more about the risks, let us know more about the city of Gotham. The city is an environment where people share services. These services can be infrastructure, platforms, software, data, APIs, and anything one can think of sharing in public/private. This cloud computing concept makes it super easy for people planning to build their city infrastructure. With this idea, the cost-benefit, first-time investment, maintenance, computation, and storage capability (hardware) are tangible. Description. Forrester, the research company, quotes cloud computing as:
“A standardized IT capability (services, software, or infrastructure) delivered in a pay-per-use, self-service way. Research coverage includes cloud security.”
Types of Risks of Cloud Computing
The invaders of Gotham City can be anyone with any motive behind it. Let us look at the different types of risks over Cloud computing and the buckets we can categorize them into.
1. Privacy
The risks below may result from malicious activities intended to attack private data.
- Controlled Access: If the people/organization tries to store confidential data in the cloud, the cloud’s true nature provides access to the service provider organization.
Analogous Situation: Gotham City’s government has all data and access.
- Segmentation: By the true nature of the subscription policy of cloud computing, there would be many subscribers, thus making one organization’s data prone to another.
Analogous Situation: The lack of proper security measures in the Gotham government’s data poses a risk of exposing individuals’ health issues to the public, which is undesirable.
- Risks with Sub-letting Services: With the growing popularity of service providing cloud computing genre, the organization’s cloud services’ layers are built from other service-provider organizations. Thus, the contractual agreement may not be fully transparent to end customers, leaving them in blind spots.
Analogous Situation: The government of Gotham has an MoU (Memorandum of Understanding) with some other governing body, which the citizens are unaware of, thus turning a blind eye to their data usage.
- Ownership Claim: If the agreement is not well-read, the data’s ownership can be unknowingly transferred to the service-providing organization.
Analogous Situation: If citizens don’t carefully read the agreement, someone can access personal data, and there are chances that this data can be used for unlawful activities.
2. Availability
- Service Disruption: This can be attributed to any fault in the internet connection, as all cloud computing transactions are done over the internet. This can be either service quality degraded or an outage as a whole.
Analogous Situation: The citizens depend on electricity for all their everyday needs. And if there is no electricity in Gotham, the whole idea of growing the city is foiled.
3. Changes
- Change in Service: Due to the volatile market, there may be the acquisition or closure of a service provider, thus leading to the unavailability of the service on short notice.
Analogous Situation: The government may come and go, and when they go, the data might not be available temporarily or permanently depending on the next government’s plan.
- Return on Investment: The whole intuition behind cloud computing is to be cost-effective. But due to unforeseen circumstances, the subscription cost is high; it might jeopardize the entire purpose of cloud computing.
Analogous Situation: The service subscription cost is so high that each citizen’s allocated budget for these services renders them non-cost effective.
4. Compliance
- Audit: The service provider organization might not follow the external audit process, thus leading to a vulnerable position for the end customers.
- Storage Location: Since the data for the services reside in hardware, and the location of that storage device is unknown, it might risk the country’s sensitive data getting leaked by rival countries.
- Notification: The lack of proper and transparent communication regarding a breach to the end customer puts them at risk, as they may not be aware of the potential harm caused.
Advantages of Cloud Computing
In addition to the risks associated with cloud computing, it is worth considering whether it lives up to the hype. Let us see the advantages of cloud computing and finally get an argument on its viability.
- Reduced Costs
- Scalability
- Keep up-to-date with the technology.
- Storage space optimization
- Flexibility of work
- Quick up time from disruption
It depends on the organization to go for a trade-off between the advantages and the risks they pose. There are different channels for risk mitigation to truly value cloud computing effectiveness, which can be dealt with as a new topic altogether. But, to add a flavor of mitigation is to determine appropriate controls for the service provider in terms of the contractual agreement and follow up from time to time on the service provider’s practices.
Mind Map of Cloud Computing
Conclusion
Having a proper mitigation channel will enhance the usage of cloud computing with appropriate security and privacy measures, aligning with the original intention behind its creation. It might be possible that a few pieces of data, e.g. Health/Finance data, need to be handled with care in the cloud. The organization planning to move to the cloud needs to have a full comparative report before the advancement.
Recommended Articles
This is a guide to the Risks of Cloud Computing. Here we discuss the introduction, types of risks of cloud computing, and advantages. You can also look at the following articles to learn more –