Introduction of Public Key Infrastructure
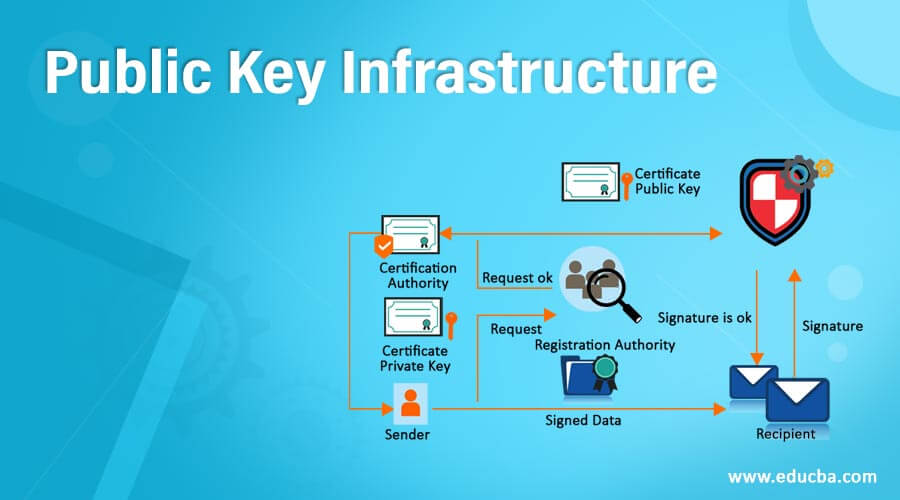
Public key infrastructure is the most popular technology which gains the focus of modern security mechanisms on the internet. It is closely related to asymmetric key Encryption technique which includes message digest, digital signature, and encryption services. To establish, maintain, and grow a public key infrastructure, commitments, substantial investment, and efforts. A digital certificate is required to enable all services. It acts as a passport on the web.
In this article, we are going to discuss public key infrastructure with a digital certificate and its standards like PKIX, PKCS, and XML.
Top Public Key Infrastructure
Here we discuss the public key infrastructure:
1. Digital Signature
A digital certificate is a small computer file that specifies the relationship between a user and it’s the public key. The X.509 standard is used to define the structure of a digital certificate. The digital signature field is as follows
- Version: It identifies the particular version of X.509 protocol which is used for a digital certificate
- Certificate Serial Number: It defines a unique integer number, which is usually generated by CA (certification authority).
- Signature Algorithm Identifier: It defines the algorithm which CA used to sign the digital certificate.
- Issuer Name: It identifies the Distinguished Name of the CA who created and signed a certificate.
- Validity: It contains two value Not Before and Not after, which specify the time frame within the certificate should be considered as valid.
- Subject Name: It identifies the distinguished name of the user to whom a certificate is issued.
- Subject Public Key Information: It contains the subject’s public key and algorithm related to that key.
2. PKIX
PKIX stands for Public Key Infrastructure X.509. X.509 is a standard that defines the structure, format, and fields of a digital certificate. It also defines the procedure used for distributing the public keys. To extend the standard and make them universal, IETF (Internet Engineering Task Force) formed PKIX (Public Key Infrastructure X.509), a working group. It extends the basic concept of X.508 standard and specifies how digital certificates can be implemented over the internet. Public Key Infrastructure X.509 provides the following services
- Registration: It is a process where the subject makes itself known to CA. Usually, RA performs this task.
- Initialization: It deals with basic problems like methodologies of verifying end entity is talking to right CA.
- Certification: It is a process where CA creates a digital certificate for the end entity and returns it to the end entity. It also maintains a copy of the digital certificate for ita own records.
- Key Pair Recovery: Keys used for encryption are recovered for decrypting the old documents.
- Key generations: Public Key Infrastructure X.509 specifies that the end entity should be able to generate both public and private key pairs.
- Key update: It is a process where the old expired key pair is updated with a new valid key pair.
- Cross certification: It provides trustworthiness, so that end entity can cross verify each other.
- Revocation: Public Key Infrastructure X.509 provides revocation to check the status of digital certificates.
3. PKCS
PKCS stands for Public Key Cryptographic Standard, which is a model developed by RSA laboratories. The aim behind PKCS development is to standardized public key infrastructure. The standardization is in many respects like formatting, algorithms, and APIs. It helps many organizations to develop and implement interoperable public key infrastructure solutions. public-key cryptographic standards provide 15 standards which are as follows:
- PKCS#1: It defines basic formatting rules for RSA public key function.
- PKCS#2: It defines message digest calculation.
- PKCS#3: It defines a mechanism for the Diffie Hellman key agreement algorithm.
- PKCS#4: It is merged with PKCS#1.
- PKCS#5: It defines a method for symmetric key encryption.
- PKCS#6: It defines a syntax for extending the digital certificate.
- PKCS#7: It defines a syntax for cryptographic message standards.
- PKCS#8: It defines a syntax for private key information.
- PKCS#9: It defines a selection of attributes types for extending digital certificates.
- PKCS#10: It defines a syntax for the certificate requests.
- PKCS#11: It defines cryptographic tokens. This standard is also known for Cryptoki.
- PKCS#12: It defines a syntax for exchanging personal information like a private key, digital certificate, etc.
- PKCS#13: It deals with a new cryptographic standard mechanism.
- PKCS#14: It defines a standard for the pseudo-random number generator.
- PKCS#15: It defines a standard for cryptographic token information.
4. XML Security
XML stands for Extensible Markup Language are at the center stage of the modern world of technology, firms the backbone of the upcoming technologies. XML key management specification (XKMS) is divided into two parts – XML encryption and XML digital signature
XML Encryption
XML encryption Steps involved in XML encryption
- Select the XML which need to be encrypted.
- Convert data in canonical form.
- Encrypt the result with a public key.
- Send the encrypted XML document to the intended receiver.
XML Digital Signature
Elements involved in XML digital signature are as follows
- Signedinfo: It contains signatures itself.
- Canonicalization Method: It specifies the algorithm used to canonicalize the Signedinfo.
- Signature Method: It specifies the algorithm used for transforming canonized Signedinfo.
- Reference: Ut defines a mechanism to calculate the Message Digest.
- KeyInfo: It defines key which is used for validating a digital signature.
- Transforms: It defines the operation that needs to be performed before calculating a message digest.
- Digest Method: It defines an algorithm that is used for message digest calculation.
- Digest Value: It contains the message digest of the original message.
Recommended Articles
This is a guide to Public Key Infrastructure. Here we also discuss the introduction and top public key infrastructure which include, digital certificate, PKIX, and XML stands, etc. You may also have a look at the following articles to learn more –


