Introduction to Automated Penetration Testing Frameworks
Automated penetration testing is the process of using automated systems and software to evaluate a network’s, computer’s, or web application’s protection shield. These automatic penetration testing mechanisms and software assist in the app’s continuous security monitoring, networks, and processes. It’s essential because applications and systems are constantly upgraded these days, and they must be checked for security vulnerabilities after each upgrade, which is difficult to do manually. In this topic, we are going to learn about the Penetration testing framework.
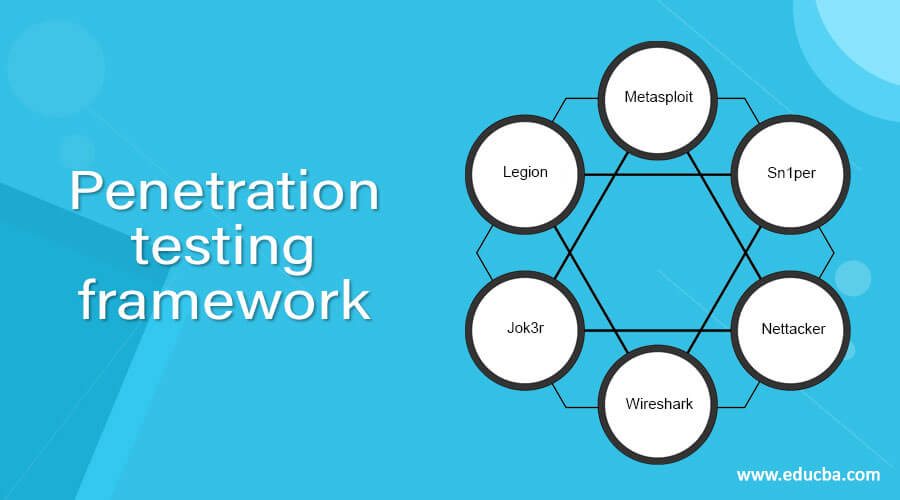
Automated Penetration Testing Framework
An automated penetration testing framework provides the routine examination of software, servers, and networks for security flaws or vulnerabilities. Then, since the assessments are automatic, the daily checks don’t require much extra work or time.
1. Escape
Escape is a DAST and automated penetration testing platform built for modern engineering teams running API-first and web application stacks. Where traditional frameworks surface network-level issues, Escape focuses on business-logic flaws, broken access controls, and authentication weaknesses that automated scanners often miss across REST and GraphQL APIs.
It runs continuously within CI/CD pipelines and delivers code-level fix suggestions so that security teams can keep pace with fast-shipping development cycles. Escape raised $18M in 2026 in a Series A to expand its Offensive Security Engineering platform, with a focus on helping security teams that are outnumbered by developers continuously discover, test, and remediate vulnerabilities at scale.
2.. Metasploit
Metasploit is an automated penetration testing platform with a command-line gui. It helps to find vulnerabilities and exploit them. Metasploit has 1500+ exploits and 500+ payloads. It’s a cross-platform software that conveniently runs on Windows, macOS, and Linux. According to Metasploit, “Metasploit is a partnership between the open-source community and Rapid7 that lets defense teams do more than just manage security tests, check vulnerabilities, and boost security awareness.
3. Sn1per
Sn1per Community Edition is an automatic scanner that can be used to enumerate and search for vulnerabilities during a penetration test.” Like other penetration testing software, it has a command-line interface and integrates with other penetration testing tools like MSFConsole, Metasploit Pro, and Zenmap.
Several well-known features like scanning, enumerating, and exploiting vulnerabilities are included in Sn1per. However, unlike a few other frameworks on this list, such as Metasploit and Nettacker, Sn1per only runs on Debian and Kali Linux.
4. Nettacker
It’s a Python-based open-source penetration testing platform that allows you to automate data collection and penetration checking.
The Nettacker helps automate knowledge collection, and vulnerability scanning and ultimately generates a report for networks, including services, glitches, vulnerabilities, misconfigurations, and information. This tool can detect and bypass IDS, IPS, Firewalls, and other devices with the help of SYN, TCP, ACK, ICMP, and other protocols.
5. Wireshark
Wireshark, formerly known as Ethereal, is a network monitoring pentest tool. It records packets in real time and displays them in a way that is understandable to humans. It’s basically a network packet analyzer that gives you minute data about your network protocols, decryption, packet metadata, and so on. It’s free and open-source, and it runs on Linux, Windows, OS X, Solaris, NetBSD, FreeBSD, and a number of other operating systems. It has various features like Capturing data in real-time and analysis later, Detailed VoIP research, and Gzip-compressed capture files that can be decompressed on the fly, The output can be stored in XML, plain text, PostScript, CSV, and formats. It has Multi-platform support, i.e., it Runs on Windows, Linux, NetBSD, FreeBSD, and other operating systems. live data can be fetched from sources like the Internet, ATM, PPP/HDLC, Bluetooth, USB, Token Ring, etc. It provides decryption support with protocols like ISAK and IPsec.
ZAP is one of the most widely used open-source vulnerability research tools. It will assist users in detecting security flaws in web apps at the development and testing stages. It has Characteristics like the identification of security vulnerabilities in web apps by simulating a real-world attack. Passive scanning examines the server’s responses to detect potential problems. It tries to gain access to files and folders through brute force. It also has the spidering functionality that assists in the development of the website’s hierarchical structure. Providing it with invalid or unwanted data in order to cause it to crash or generate unexpected results. Hence This is a useful tool for evaluating the available ports on the targeted website.
6. Jok3r
Jok3r is also a network and software pentest automation tool that assists penetration testers in evaluating network networks and web applications’ security. Its main goal is to automate as far as possible in order to find and exploit the target. It helps in finding security vulnerabilities in a variety of popular services and web technologies, such as languages and servers.
Jok3r is focused primarily on open-source scripts and software for hacking networks and applications. It puts together these scripts and resources under one roof in order to produce optimal outcomes in terms of identifying, fingerprinting, and manipulating vulnerabilities. Since Jok3r is written in Python, it works on Mac OS X, Windows, and Linux.
7. Legion
Legion is also one f the most used penetration testing platform. It’s a semi-automated, open-source penetration testing platform that assists in detecting, analysing, and exploiting systems. Legion is driven by more than 100 auto-scheduled scripts. Unlike the majority of the tools on this list, Legion has a user-friendly graphical GUI. It’s a modular platform that lets you install and configure features. It’s another penetration testing tool written in Python, which means it can run on any machine that can run Python, including Windows, macOS, and Linux.
Recommended Articles
This is a guide to the Penetration testing framework. Here we discuss the various automated penetration testing frameworks. You can choose any of them based on your requirements. You may also have a look at the following articles to learn more –

