Updated May 30, 2023
Introduction to Daisy Chain Topology
The structure of the network is formed by connecting one or many nodes or computers. It depends on the requirement that any extra node is mandatory for the network arrangement. The addition of a node to a network topology based on the structure and requirement is termed as daisy-chaining. The name daisy chain is derived from the virus hoax. In this article, the importance and application of the daisy chain network are briefly discussed.
What is Daisy Chain Topology?
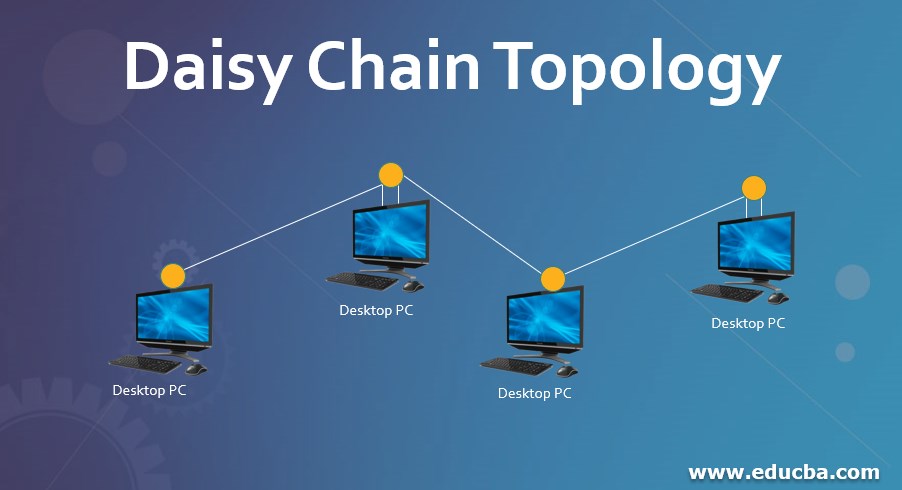
In a daisy chain network, one network node is connected to the next node in a computer network. It is used to transmit the message down the line for a partway of a computer network. once the message is transmitted from the node, it goes down the passage until the concerned message reaches the destinated node. There are two types of daisy chain networks such as linear daisy chain and ring daisy chain. It can be connected in a linear structure or ring structure.
It is said to be linear if the first node and last node of a network is not attached. If the first node and last node of the network are connected it forms a ring structure daisy chain topology. In a linear structure, the flow of the message is in one direction from one system to another. But in a ring structure, the flow of the message is bidirectional. A linear daisy chain structure is the same as of an electrical series, where if any attack on one node affects the other part of the circuit.
It is minimum versatile as the attack on one network affects the rest of the entire system leading to a shut down of productivity. But in a ring structure, the data can be transmitted in bidirectional and send in both directions. It prevents one node failure from eliminating the affected parts of the network. The network topology includes a hub that transmits the passage from one system to another. For example, a star topology that manages at times of multiple node attacks without affecting the productivity of working systems.
Why we Use Daisy Chain Topology?
There are many advantages in the daisy chain network. It doesn’t create any complex caballing networks and only limited wiring is needed for the function of multiple computers. It cleans up space by reduces the complexity of cluster formation. It uses only short cables that have a minimum length to connect ports and monitors. So it reduces the total length of wire and only minimum PVC quantity is required which is cost-effective. The connection between monitors is easy to implement even though it is hosted in a remote area. Because only one display cable is required to connect the computer and port.
A computer graphics board is required to have a single display output port instead of several boards. So it makes simple to implement the daisy chain network for small personal computer users and laptop users as they require only limited outputs. The daisy chain network is a reliable system because the cables cannot be pulled out accidentally unlike some other complex cable systems. After all, the clip of the display port is connected to the terminal which is significant in view the sensitive information. The daisy chain doesn’t impact the refresh rate of a monitor, which implies that the clarity of the image doesn’t get degraded as they are connected directly to the personal computers.
The example of a daisy chain interface is firewire and small computer system interface which enable the computer to interact with peripheral components such as CD-ROM, disk, tape drives, scanners and printers which works faster and flexible than existing interfacing components. It is popularly known for its simplicity and scalability.
According to the requirement, we can add or remove multiple nodes from the network. The daisy chain system can be extended as long as possible but it is not applicable in the system if the nodes are scattered all over the particular geographical region. So in those situations, the cables are connected as a zig-zag all around the network and become huge when compared with the actual distance between the nodes. This slows down the operation for the users located at the opposite end of the system.
Importance of a Daisy Chain Network
The small computer system interface is the best example of a digital system that follows a daisy chain network which implies a structure of a bus. As it is a model of a bus, it should be terminated by using an interface option to internally terminate the device or it can be done by plugging a terminator to the last component of the system. The MIDI is usually implemented particularly as a daisy chain component.
It is standard for a device to operate on OUT or THRU port which is used for chaining. The THRU port passes the information with minimum delay and the OUT port transmits the entire regenerated signals which may add, change or remove messages in case of any delay. The difference in the arrival of signals may get varied if the chain is long and there are chances of breakage which leads to the unreliable system and so some of the systems are built with daisy chain capability.
The JTAG and Thunderbolt interfaces support daisy chain networks when it is built-in personal computers and RAID arrays. For analog signals, the connections are similar to bus and can be deployed in repeaters or amplifiers within the network to respond to attenuation. But in digital signals, it cannot be modified as they are discrete.
Conclusion
Hence the daisy chain network is a simple and reliable network that has its specified applications and deployment. The chaining of multiple components of the UART port to each other to behave cooperatively and helps to seize the activation of the bus at any time in case of an emergency preventing the rest of the network without impacting its productivity.
Recommended Articles
This is a guide to Daisy Chain Topology. Here we discuss the Why we use Daisy Chain Topology along with the importance of its network. You may also have a look at the following articles to learn more –


