Updated August 16, 2023
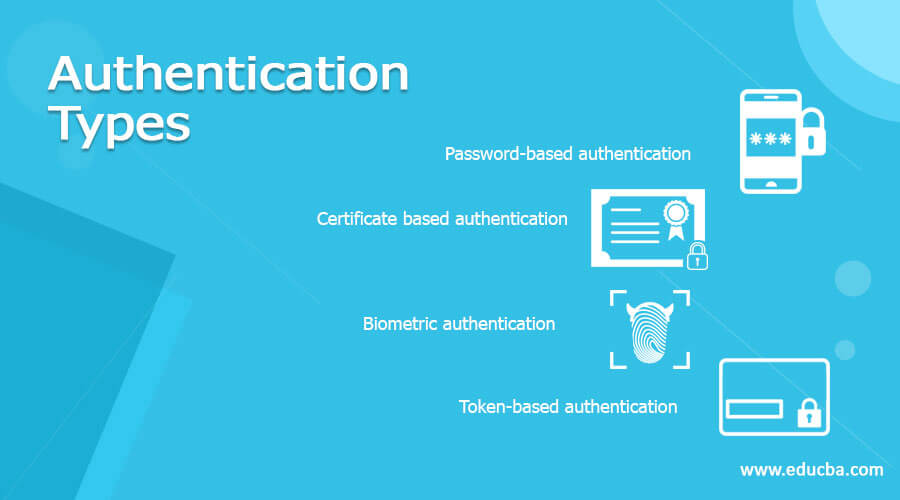
Introduction to Authentication Types
Authentication is the process of identifying users that request access to software, network, or device. Access control authenticates user identity using username and password. Authentication enables the user or computer system to authenticate the user to the application at the other end and based on the results, it decides whether to allow or reject the user. It provides support for data integrity and authentication of IP data packets. The authentication process is divided into various types based on its process. It can be done in various ways. In this article, we are going to discuss the types of authentication.
Authentication Types
Types of authentication are as follows:
1. Password-based Authentication
Password-based authentication is the most common form of authentication. It is a string of alphabets, special characters, numbers, which is supposed to be known only to the authentic person that is being authenticated. A clear-text password is the simplest password-based mechanism. in this mechanism, the user id and password are assigned to the user. for securing purposes, the user changes the password periodically. the password is stored in the database against the user ID in clear text format. During the authentication process, the first application prompt a screen for user ID and password. then user enters his/her user ID and password and press the OK or sign in button. after clicking OK, both user ID and password travel to the server in clear text format. server checks the user database to see if this particular user ID and password exist or not. this validation is done by the user authenticator program. these programs check the entered user ID and password against the stored user database and based on the success or failure it returns a result.
2. Certificate-based authentication
The digital certificate is a part of big word Security. It has information about the key, the owner, and the digital signature of a third-party entity that has verified the certificate. If the certificate is valid, the software verifying the certificate trusts the issuer and can be used as a key for communicating securely. Certificates are provided by third-party organizations known as Certificate Authorities (CA) like VeriSign, GeoTrust, and DigiCert. The common format for public-key certificates is defined by X.509. Digital certificates act as trust documents. It states that you are the one who has transformed the information by digitally signing the information. It helps the recipient in identifying the authenticity of the sender.
3. Biometric authentication
Biometric authentication is a popular authentication mechanism that is getting more attention from the public. You can see that we are using biometric authentication everywhere from unlocking the phone with fingerprint or face lock to office attendance. The application of biometric authentication is not limited to phone and office, they are used in various fields to accomplish security. First user’s sample (fingerprint, face, retina, voice, etc.) Is created and stored in the user database. Then at the time of authentication, the user needs to provide the sample of the same which he or she provided at the time of creation. This is usually sent across an encrypted session to the server. At the server-side, the user’s current sample is decrypted and compared with the stored sample in the database. If these two samples are matched to the excepted degree on the basis of particular values of biometrics the user will be considered as valid, otherwise, it will be considered as invalid. Two perform, biometric authentication two techniques are used physiological techniques and behavioral techniques. Physiological technique makes use of face, fingerprint, voice, retina, Iris. In, behavioral technique, person’s behavior is observed to ensure that he or she is not trying to claim to be someone else. It makes use of keystrokes and signature.
4. Token-based authentication
Authentication tokens are an alternative for the password. It is a small device that is used to generate a new random value every time. This random value becomes a basis for authentication. The small devices are typically of the size of small key chains, calculators, or credit cards. Usually, an authentication token has the features such as Battery, Liquid Crystal Display (LCD) for output display, Processor, Small keypad to enter information (It is optional), Real-time clock (optional). Each authentication token is preprogrammed with a unique number called a random seed or seed. This random seed ensures that every value generated by an Authentication token is unique. There are two types of authentication tokens. One is Challenge/ response tokens, a combination of techniques is used. The seed is preprogrammed inside the authentication token, this seed is kept secret and should be unique. In this tokens, the seed becomes an encryption key. Second is a time-based token, in which server needs to send any random challenge to the user. The goal behind this is to use the time as a variable input to the authentication process, in place of the random challenge.
Conclusion
In this article, we have discussed the four types of authentication such as password-based authentication, certificate-based authentication, biometric authentication, and token-based authentication. We have discussed its working in detail. Hope you enjoyed the article.
Recommended Articles
This is a guide to Authentication Types. Here we discuss the Introduction and 4 Types of authentication along with a detailed explanation. You may also have a look at the following articles to learn more –