Updated April 13, 2023
Introduction to Kubernetes external secrets
The Kubernetes external secrets are defined as, the external secrets is an operator in Kubernetes which combines the external secrets management systems in which we can say that it is a collection of customized resources of API that gives the user-friendly procession for external API, and it can be used to read the information from external APIs, and it can spontaneously administer the values as Kubernetes secrets, it allows us to make use of external secrets management system to safely put on the secrets in Kubernetes and also it can able to read further information regarding the design and simulation of the Kubernetes external systems.
What are Kubernetes’ external secrets?
The external secrets allow us to make use of the external management systems and to append the secrets safely in the Kubernetes; it can also read the extra information which is related to design and inspiration for the Kubernetes, the secret in the external secrets is an entity that carries a small amount of delicate data like password, token or key in which that type of the information can be stored in the identification of the pod hence we do not need to involve the private data in our application code when we try to generate the secrets with kubectl then it can generate the ‘-f secret.yaml’ to store that in the ‘etcd’ otherwise, we have to define the encryption provider if we try to define the provider previous t the secret to being stored and then the values can be yielded in the API, kubectl can be used to get the secrets.
The Kubernetes can have the in-built objects for supporting the secrets, which can also be called a secret; it provides an indicative API so that it can be simple for the application pod to access the secret data and there is no need for any special code, the secret objects does not manage the storage of external secrets management system.
Using external secrets
- By using the below command, we can able to add the external secrets to our cluster,
"kubectl apply -f https://raw.githubusercontent.com/godaddy/kubernetes-external-secrets/master/external-secrets.yml"- Below is the object type in which the External secrets has been handled by using them,
"kubectl -n deers-and-bears get es"Suppose we want to transform the secret object into an external secret. In that case, it uses the Kubernetes secrets CLI so that the transformation gets easier. That can be done by using the kubectl command, which can be used to load the data in secret so that the external secret object has been generated.
Kubernetes external secrets examples
Different examples are mentioned below:
Example #1
apiVersion: v1
kind: Secret
metadata:
name: rat-and-rabbit
type: Opaque
data:
password: b38uXfp=In the example, the secret object has been used to store the password of the database.
Example #2
apiVersion: 'v1'
kind: ExtrenalSecret
metadata:
name: deers-and-bears
secretDescriptor:
backendType: secretsManager
data:
- key: deers-and-bears/mysql-password
name: passwordIn this example, the ExternalSecret can be used to identify the secret management system, and data can be carried in an array.
Kubernetes external secrets design
With the help of the Custom Resource Definition, the object of the external secret has been added by the external secrets, and for adding the external secret controller that needs to write in the node.js which that can contrivance the bearing of the objects itself.
The external secret controller can come after the Kubernetes objects which follows the pattern, the objects are maybe as development in which user can define the state of the external secret objects, the controller can generate the supporting object to stick out at the state, the controller can support the object of an external secret object, and it can also bring the secret information from the particular external secret management system, and it can mechanically generate the local secret object for carrying the data.
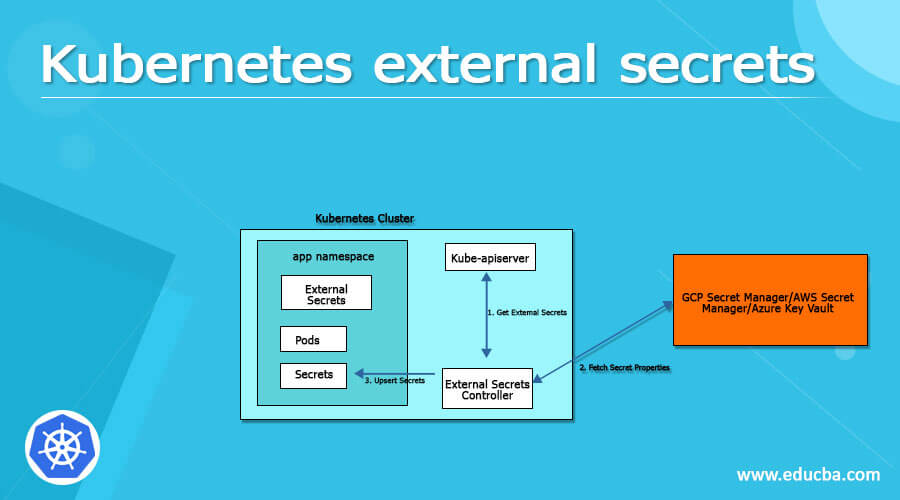
Simply we can say that the design of the external secret,
- External secrets can be added to the cluster.
- The controller can give the external secrets with the help of Kubernetes API.
- The controller can use the external secret for fetching private data.
External secret management systems
The Kubernetes secret can reserve private objects like passwords, tokens, and keys to provide security in our cluster, I which secrets can provide more flexibility in the life cycle of the pod, and it supports the delicate data which can be used in which that can overcome the risk of revealing data to the unauthorized user.
- The secrets are the objects of the namespace.
- The secrets can be scaled as environmental variables that can be utilized by the container available in the pod.
- The secret data has been put away in tmpfs in nodes.
- API server can keep the data secret like plain text that is in etcd.
- The size of the one secret might be 1 MB.
- Creating a secret:
The username.txt and password.txt has been created by using the below command,
"echo -n 'root' > ./username.txt""echo -n 'Npgs' > ./password.txt"- List secret:
The list of secrets has been created by using the below command,
"kubectl get secret/db-serds"And the output will be given in table format.
- View secret:
The secrets have been viewed by using the below command,
"kubectl describe secret/db-serds".And the output will something like,
Name: db-serds
Namespace: default
Labels:
Annotations:
Type: Opaque
Data
====
password.txt: 12 bytes
username.txt: 5 bytes- Using yaml file:
The secret can be used by using the workloads in two different ways, which by identifying the objects,
"echo -n 'root' | base64"- The secret can be used by using the workloads in two different ways by identifying the objects.
Conclusion
This article concludes that the external secrets will allow us to manage the external secret management systems, which can read the information from the external API. We have also seen the design with examples, so this article will help us understand the concept of external secrets.
Recommended Articles
We hope that this EDUCBA information on “Kubernetes external secrets” was beneficial to you. You can view EDUCBA’s recommended articles for more information.

