What is Incident Response?
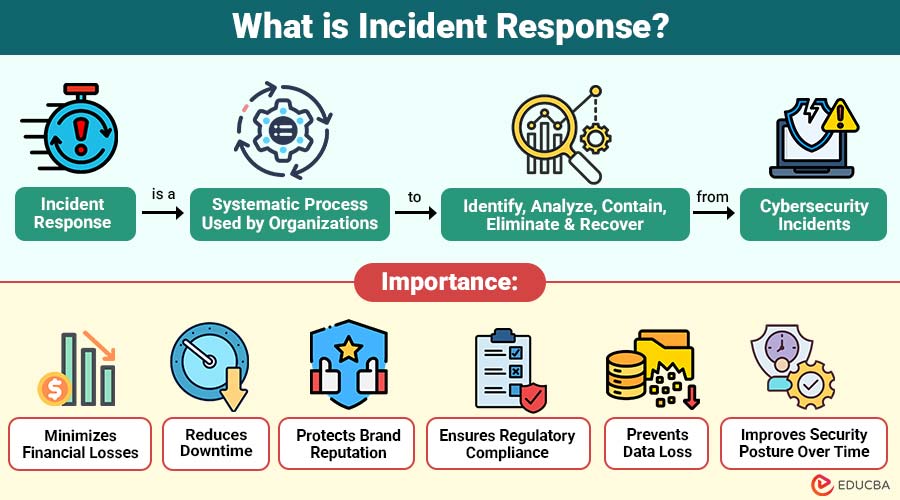
Incident Response (IR) is a systematic process used by organizations to identify, analyze, contain, eliminate, and recover from cybersecurity incidents. It involves coordinated efforts by IT teams, security analysts, management, and, sometimes, legal authorities.
The primary goals of incident response are:
- Reduce the impact of security breaches
- Prevent further damage
- Ensure business continuity
- Preserve evidence for investigation
- Improve security posture for the future
Table of Contents:
Key Takeaways:
- Incident Response provides a structured approach to efficiently detect, contain, and recover from cybersecurity incidents.
- A good plan for handling attacks helps a company lose less money, keeps work running, protects its reputation, and avoids breaking rules.
- Using standard frameworks and clear steps helps manage security incidents in a consistent, organized, and effective way.
- Continuous improvement through lessons learned strengthens defenses and enhances organizational resilience against evolving cyber threats.
Why is Incident Response Important?
Here are the key reasons why Incident Response is important for organizations:
1. Minimizes Financial Losses
A structured response quickly contains security incidents, reducing recovery costs, preventing revenue disruption, and avoiding expensive legal penalties or ransom payments.
2. Reduces Downtime
Good incident management fixes systems quickly, keeps the business running, and reduces disruptions to work and customer service.
3. Protects Brand Reputation
Quick and clear responses to security breaches earn trust, show responsibility, and protect the organization’s reputation over time.
4. Ensures Regulatory Compliance
Incident response helps organizations meet legal reporting obligations, comply with industry regulations, and avoid compliance fines under data protection laws.
5. Prevents Data Loss
Finding and stopping threats fast keeps data safe, protects privacy, and keeps people trusting the organization.
6. Improves Security Posture Over Time
After a cyberattack, the organization reviews what happened, finds weak points, improves security, upgrades monitoring, and becomes stronger against future threats.
Types of Security Incidents
Organizations may encounter different types of security incidents, including:
1. Malware Attacks
Malicious software, including viruses, trojans, spyware, and worms, infects systems, disrupts operations, steals sensitive information, or damages critical infrastructure resources.
2. Phishing Attacks
3. Ransomware
Attackers encrypt critical business data and demand ransom payments in exchange for decryption keys, threatening permanent data loss or exposure.
4. Data Breaches
Unauthorized individuals gain access to confidential customer, employee, or financial data, leading to privacy violations and regulatory penalties.
5. Insider Threats
6. Denial-of-Service Attacks
Attackers flood systems, servers, or networks with excessive traffic, overwhelming resources, and causing service outages for legitimate users.
Incident Response Lifecycle
The process generally includes six key phases:
1. Preparation
Preparation is foundation of effective incident response. This phase involves:
- Developing an incident response plan (IRP)
- Defining roles and responsibilities
- Conducting training and simulations
- Implementing monitoring tools
- Creating communication protocols
- Maintaining backup systems
Organizations often align with the SANS Institute model to structure their preparation phase.
2. Identification
In this stage, the organization determines whether a security event qualifies as an incident. Activities include:
- Monitoring logs and alerts
- Investigating unusual activity
- Confirming attack presence
- Documenting initial findings
Security tools such as SIEM systems help detect anomalies quickly.
3. Containment
The goal of the containment phase is to stop additional harm. There are two types of containment:
- Short-term containment: Isolate affected systems immediately.
- Long-term containment: Apply temporary fixes while maintaining operations.
Quick containment is crucial to avoid lateral movement within networks.
4. Eradication
Once the threat is contained, the root cause must be eliminated. This may include:
- Removing malware
- Deleting compromised accounts
- Patching vulnerabilities
- Updating configurations
Failure to eradicate can result in recurring incidents.
5. Recovery
Recovery ensures systems are restored to normal operation. This stage includes:
- Restoring from backups
- Testing systems
- Monitoring for reinfection
- Reintegrating systems into production
Careful monitoring is essential before declaring the incident resolved.
6. Lessons Learned
The final stage focuses on improvement. Teams conduct a post-incident review to:
- Identify weaknesses
- Update policies
- Improve detection capabilities
- Strengthen controls
- Document insights
Continuous improvement makes future responses more effective.
Incident Response Tools
Several tools assist in detecting and responding to incidents:
1. SIEM Tools
Splunk and IBM QRadar are examples of SIEM systems that gather, relate, and examine log data to identify security events in real time.
2. Endpoint Detection and Response
EDR tools like CrowdStrike Falcon constantly watch computers and devices, detect unusual activity, and help security teams quickly investigate and stop threats automatically.
3. Firewalls and IDS/IPS
Firewalls and Intrusion Detection/Prevention Systems monitor network traffic, block unauthorized access, detect malicious activity, and prevent potential security breaches.
4. Digital Forensics Tools
Digital forensics tools analyze compromised systems, preserve evidence, trace attack origins, and support legal investigations after cybersecurity incidents occur.
5. Backup and Recovery Tools
Incident Response Frameworks
Organizations often follow structured frameworks such as:
1. National Institute of Standards and Technology Framework
It gives step-by-step guidance to handle cyberattacks, including preparing in advance, finding threats early, stopping the attack, removing the problem, restoring systems, and learning from the incident to improve future security and strengthen overall protection.
2. SANS Institute Model
Provides a useful six-step incident handling procedure with a focus on security teams’ preparation, identification, containment, eradication, recovery, and lessons learned.
3. ISO/IEC 27035 Guidelines
International standard providing comprehensive guidance for incident management processes, coordination, reporting, and continual improvement within information security management systems.
4. MITRE ATT&CK Framework
Knowledge base of adversary tactics and techniques helping organizations understand attacker behavior, improve detection capabilities, and strengthen defensive strategies.
Key Components of Incident Response Plan
A well-documented IRP should include:
1. Incident Classification Criteria
Defines severity levels, impact categories, and prioritization guidelines to assess incidents and quickly determine appropriate responses accurately.
2. Escalation Procedures
Outlines clear steps for notifying management, technical teams, and external authorities when incidents exceed predefined severity thresholds.
3. Communication Strategy
Specifies internal and external communication protocols, designated spokespersons, and messaging guidelines during security incidents or crises.
4. Legal Considerations
Covers legal rules, contracts, data protection laws, and working with lawyers during investigations.
5. Evidence Handling Process
Defines secure evidence collection, documentation, preservation methods, and chain-of-custody procedures for forensic and legal purposes.
6. Disaster Recovery Integration
Ensures coordination between incident response and disaster recovery teams to restore systems and maintain business continuity.
7. Regulatory Reporting Requirements
Challenges in Incident Response
Organizations face several challenges:
1. Lack of Skilled Security Professionals
Shortage of experienced cybersecurity experts limits effective threat analysis, rapid containment, and strategic decision-making during critical security incidents.
2. Delayed Detection
Finding attacks too late lets hackers stay longer, causing more damage, losing more data, and costing more to fix.
3. Poor Communication
Inefficient coordination between teams leads to confusion, delayed actions, inconsistent messaging, and weakened overall incident management effectiveness.
4. Inadequate Documentation
Insufficient recordkeeping complicates investigations, reduces accountability, hinders compliance reporting, and prevents meaningful post-incident improvement initiatives.
5. Complex IT Environments
Diverse systems, cloud platforms, legacy infrastructure, and third-party integrations make monitoring, containment, and recovery processes more difficult.
6. Compliance Pressures
Strict regulatory requirements demand timely reporting, detailed documentation, and legal coordination, increasing operational stress during incident response efforts.
Real-World Example
In the 2017 Equifax Data Breach, 147 million people’s personal information was compromised due to an unpatched vulnerability in Apache Struts.
Lesson: Timely patching and strong incident response are critical to minimizing damage and financial loss.
Final Thoughts
Incident Response is essential in today’s evolving cybersecurity landscape. As cyber threats grow more sophisticated, organizations must implement structured frameworks, skilled teams, and advanced security tools to respond effectively. Being prepared in advance, quickly finding problems, stopping them fast, and learning from mistakes helps reduce damage, keep the business running, protect important data and systems, and maintain the organization’s reputation from new threats.
Frequently Asked Questions (FAQs)
Q1. What triggers an incident response?
Answer: Any confirmed security event that threatens data, systems, or operations.
Q2. How long does incident response take?
Answer: It depends on severity. Minor incidents may take hours, while major breaches can take weeks or months.
Q3. Who is responsible for incident response?
Answer: Typically, the security team or SOC is led by an incident response manager.
Q4. Is incident response only for large companies?
Answer: No. Small and medium businesses also need incident response plans.
Recommended Articles
We hope that this EDUCBA information on “Incident Response” was beneficial to you. You can view EDUCBA’s recommended articles for more information.

