What is Decentralized Identity?
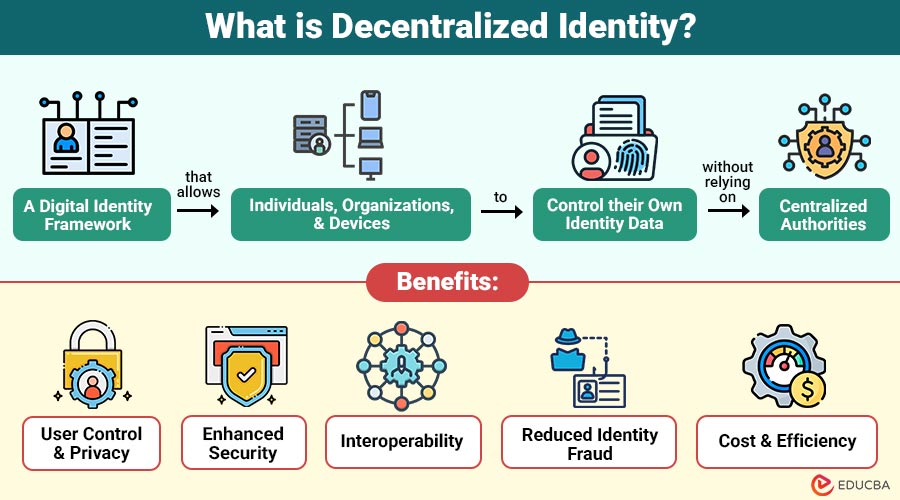
Decentralized identity is a digital identity framework that allows individuals, organizations, and devices to control their own identity data without relying on centralized authorities.
Unlike traditional identity systems, where central authority stores and manages user data, a decentralized identity:
- Is Self-Sovereign: Users own and control their personal information.
- Is Portable: Users can use the same identity across multiple platforms without re-registering.
- Uses Cryptography and Blockchain: To secure identity data, verify authenticity, and prevent tampering.
Table of Contents:
- Meaning
- Key Components
- Working
- Benefits
- Challenges and Considerations
- Real-World Applications
- Difference
Key Takeaways:
- Decentralized identity empowers individuals to own and securely manage their personal digital data fully.
- Cryptography and blockchain keep identity data secure, private, and protected from tampering or hacking.
- Users can use the same digital identity across multiple platforms without having to register or verify multiple times.
- Verifiable credentials and cryptographic proofs make it very hard for attackers to fake identities or commit identity fraud.
Key Components of Decentralized Identity
Understanding decentralized identity requires knowing its main components:
1. Decentralized Identifiers
Decentralized Identifiers are secure digital IDs on blockchains that don’t depend on any company, giving users full control over their online identity.
2. Verifiable Credentials
Verifiable credentials are digital proofs like passports or certificates that can be shared and verified without contacting the original issuer.
3. Digital Wallets
Digital wallets safely store digital IDs and credentials, letting people share only needed identity details without exposing personal information.
4. Blockchain or Distributed Ledger
Blockchain keeps a shared record that no single person controls and no one can secretly change. It helps prove information is real, track it easily, and keep it secure without needing a central authority.
How Does Decentralized Identity Work?
The workflow of decentralized identity can be broken down into simple steps:
1. Creation of Decentralized Identity
The user creates a decentralized identity with a digital wallet and registers it on the blockchain for secure identity.
2. Issuance of Credentials
Trusted organizations issue verifiable credentials, such as digital degrees or IDs, to users securely and reliably.
3. Storage in Wallet
Credentials are securely stored in the user’s digital wallet, giving complete control over personal identity data.
4. Sharing and Verification
Users share credentials when needed, and recipients verify authenticity via blockchain without contacting the issuing authority.
Benefits of Decentralized Identity
Decentralized identity offers several benefits over traditional identity systems:
1. User Control and Privacy
Individuals have full control over their personal data. They can decide what information to share, with whom, and for how long. This reduces unnecessary data exposure.
2. Enhanced Security
Verifiable credentials and decentralized identifiers are cryptographically protected, making it very impossible for hackers to obtain or alter identity data.
3. Interoperability
Systems can work across multiple platforms, industries, and regions without requiring users to create new accounts every time.
4. Reduced Identity Fraud
The use of cryptographic proofs makes it nearly impossible to forge credentials or mimic someone else.
5. Cost and Efficiency
Organizations no longer need to manage large databases of personal data, reducing storage costs and risks of breaches.
Challenges and Considerations in Decentralized Identity
While promising, decentralized identity also comes with challenges:
1. Technical Complexity
Implementing DID systems requires knowledge of blockchain, cryptography, and secure key management, which may be a barrier for organizations and individuals.
2. Regulatory and Legal Uncertainty
Different countries have varying laws regarding digital identity, data privacy, and blockchain technology. Harmonizing with legal frameworks is still ongoing.
3. User Adoption
People are used to centralized systems like Google or Facebook logins. Transitioning to self-sovereign identity requires education and trust in new technologies.
4. Lost Credentials
If user loses access to their digital wallet or private keys, they could lose access to their identity. Backup and recovery mechanisms are critical.
5. Scalability
Handling large numbers of verifiable credentials while keeping blockchain verification fast is still a technical challenge.
Real-World Applications of Decentralized Identity
Decentralized identity has practical applications across multiple industries:
1. Financial Services
Banks and fintechs verify customer identities without centrally storing sensitive data, reducing fraud, improving compliance, and enhancing overall security.
2. Healthcare
Patients decide who can see their medical records. Doctors and insurance companies can check the information quickly and safely, without searching many databases or risking patient privacy.
3. Education
4. Government Services
5. Travel and Hospitality
Travelers safely share digital credentials like passports or vaccination records, making check-ins, border checks, and identity verification faster and easier.
6. Internet of Things
IoT devices verify their identity without a central authority, making systems safer, more reliable, and less vulnerable to attacks.
Difference Between Decentralized Identity and Traditional Identity
Here is a comparison highlighting how decentralized identity differs from traditional identity systems:
| Feature | Decentralized Identity | Traditional Identity |
| Control | Users control their own data | Centralized authority controls data |
| Security | Cryptographically secure | Vulnerable to breaches |
| Portability | Usable anywhere, interoperable | Limited across platforms |
| Privacy | Users decide what to share | Often exposes unnecessary data |
| Verification | Trust verified via blockchain | Authority dependent |
| Fraud Risk | Low due to cryptographic proofs | High due to centralized databases |
Final Thoughts
Decentralized identity represents fundamental shift in how digital identities are created, managed, and trusted. By placing control back in users’ hands, it enhances privacy, security, and compatibility across platforms. Although challenges like regulation, scalability, and adoption remain, decentralized identity has strong potential to become the foundation of secure, user-centric digital ecosystems worldwide.
Frequently Asked Questions (FAQs)
Q1. Can I lose my identity if I lose my private key?
Answer: Yes, losing your private key can prevent you from accessing your credentials. Solutions such as key recovery or multi-signature wallets help mitigate this risk.
Q2. How is decentralized identity better for privacy?
Answer: Users share only what is necessary, without exposing their entire profile. There’s no central database for hackers to target.
Q3. Can businesses adopt decentralized identity easily?
Answer: Adoption requires infrastructure, integration, and education. However, standardized solutions and partnerships are simplifying implementation.
Recommended Articles
We hope that this EDUCBA information on “Decentralized Identity” was beneficial to you. You can view EDUCBA’s recommended articles for more information.
