Business Identity Theft: Strategies to Stay Secure
Business identity theft has moved past data theft. It is now impersonation at scale, emails, transactions, and even full websites. Most incidents start with exposed details and loose controls. This is where it breaks, and what actually needs tightening. This article explains how business identity theft occurs, what attackers look for, and practical ways to stop them before it is too late.
What Business Identity Theft Actually Means?
Business identity theft is simple to execute; someone operates your business without you knowing. They use your name, details, and credibility to run transactions in your name. Fraud has already played out at scale, with over a million small business identities used to apply for government-backed loans. The applications went through because the data checked out.
What Attackers Target?
- Tax numbers and EIN
- Bank account details
- Employee and executive names
- Finance or admin roles
None of this is hard to find; some of it sits on public records, and sometimes it leaks through emails, vendors, or poorly secured systems.
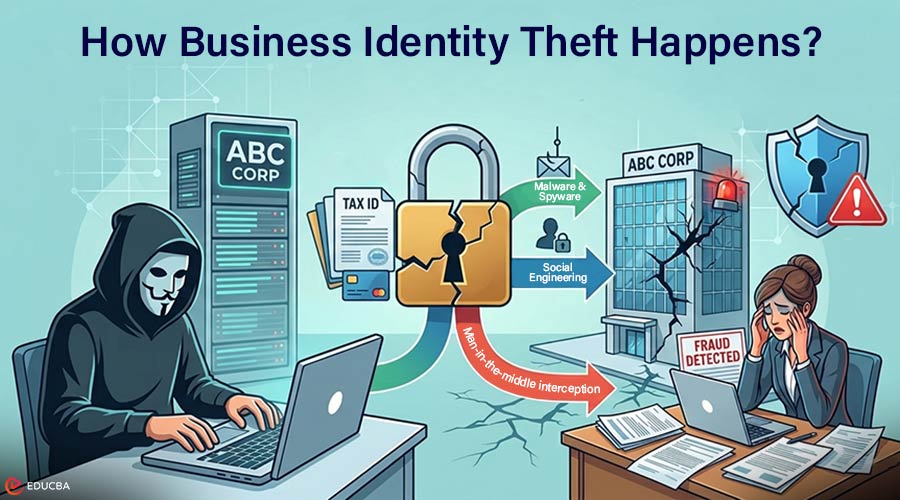
How Business Identity Theft Happens?
Attackers rarely need to break in the hard way. Most business information is already exposed if controls are loose. They combine creativity with convenience.
Common tactics they use:
- Malware and spyware: They infect devices, harvest credentials, and redirect payments. One compromised finance workstation can siphon thousands from a company account before anyone notices.
- Man-in-the-middle interception: They slip in between communications. Fraudsters quietly alter emails, payment requests, or file transfers. What appears to be a legitimate request may already have been rerouted to their account.
- Social engineering: Humans are a weak link; phishing emails, fake calls, or impersonation of executives trick employees into handing over sensitive details. CEO fraud is a classic example in which an attacker impersonates a trusted authority and convinces someone to release data or approve transactions.
Prevent Business Identity Theft with These Strategies
Stopping business identity theft is about layers, visibility, and friction where attackers expect none.
1. Lock Down IT Access
Most environments carry extra permissions that no one revisits; that is where misuse starts. Firewalls and VPNs put boundaries around your network and keep traffic encrypted, especially for remote access.
- Restrict permissions to what is required.
- Remove unused or legacy access.
- Track login patterns, failed attempts, and unusual file access
2. Protect your Brand Identity
Attackers do not always break systems. Sometimes, they just copy what already works. Lookalike domains, cloned websites, and emails that mirror your brand are enough to mislead customers, vendors, or even internal teams. Without a verifiable layer, attackers can reuse your identity with very little resistance. This is where controlled visibility becomes important. Instead of relying solely on appearance, organizations are moving toward identity-based signals that confirm authenticity. Implementing a Verified Mark Certificate for your domain introduces a verifiable layer to your brand presence in email, making impersonation attempts easier to spot.
3. Secure Communication and Digital Assets
- Sign emails so recipients can confirm the sender.
- Use SSL/TLS to keep website traffic encrypted.
- Developers sign code and executables to prove that no one has altered them.
- Unverified communication is where most impersonation succeeds.
4. Control What Outsiders See
A lot of business data sits exposed without anyone realizing it open storage, forgotten files, misconfigured access. Scan for leaked credentials and publicly exposed data regularly. Keep systems patched so known issues do not stay open. Keep backups current and at least one copy outside your primary environment.
5. Harden Credentials
Credential misuse is still one of the easiest ways in. Weak passwords, reuse, or poor storage make it easier than it should be.
- Use long, complex, unique passwords.
- Store only hashed versions, never plain text.
- Enforce adaptive MFA based on context.
- Add location or behavior checks where access carries risk.
6. Observe, Audit, and Respond
Monitor account activity, transactions, and access changes, and review them before issues escalate. Small mismatches usually show up early but get ignored. Access control also needs upkeep. When roles change or people leave, permissions often stay. That leftover access becomes an entry point.
7. Educate your Team
Most attacks land first on a person. Email, calls, internal-looking requests, that is where decisions get made.
- Train employees to question the urgency of requests, especially unfamiliar ones.
- Use real scenarios: payment requests, executive impersonation, and refund emails.
- Focus on teams handling sensitive data: finance, HR, IT, and legal.
Follow these practices to keep your business secure and defend against threats. When multiple layers work together, attackers encounter enough friction that most move on to easier targets.
What Attackers Do Once They Steal Your Business Identity?
Business Identity theft happens in ways that do not immediately stand out. Here is how it usually shows up:
- Website takeover or lookalikes: Change payment details, swap contact info, or spin up a near-identical domain. Users land on the wrong place and do not notice.
- Trademark ransom: Register your business name or logo first. Then force you to deal with it legally or financially.
- Financial fraud: Apply for credit, initiate transactions, move money. Business accounts do not always flag unusual activity right away.
- Tax fraud: File returns using your identity and collect refunds before anything gets reviewed.
None of these requires deep access to your infrastructure. It runs on believable data and timing. That is what makes it hard to spot early.
Final Thoughts
Business identity theft can hit an organization with a single lapse, an exposed account, a weak password, or an unverified email. It can exploit your brand, siphon funds, or compromise customer trust. For protection, you need to follow a practical checklist and maintain continuous monitoring. With that, you can shrink the opportunities attackers have to misuse your business identity.
Recommended Articles
We hope this guide to business identity theft helps you understand and protect your organization. Check out these recommended articles for more insights and strategies to strengthen your business security.